When importing from a Strategy Community Connectors, data import may fail and one of the following certificate errors is returned.
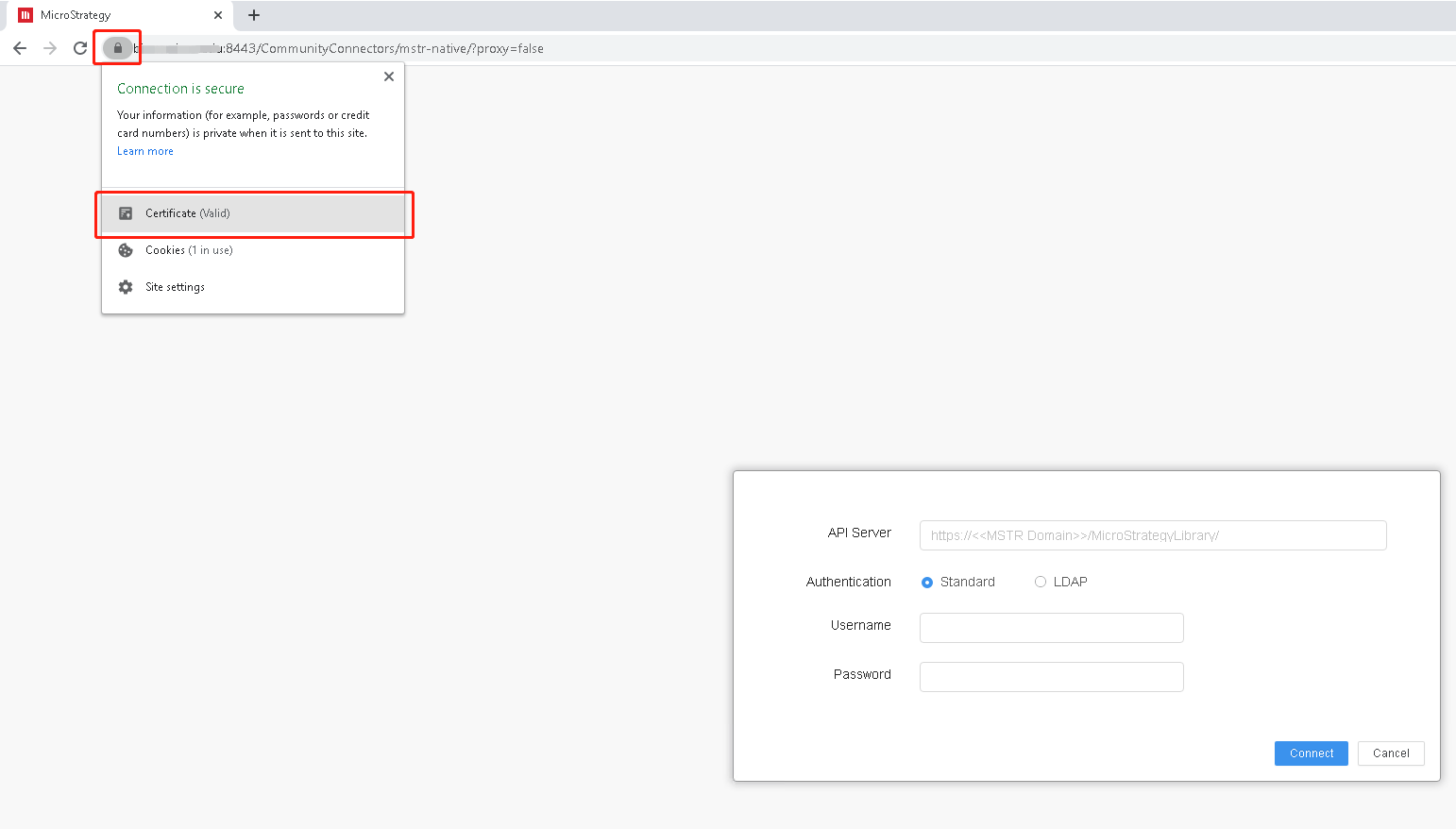
2020-09-25 11:35:35.426-04:00 [HOST:biapp][SERVER:CastorServer][PID:1984][THR:7280][Database Classes][Error][UID:B6CD16C240D4A71C4B7C2A8031C6EBE2][SID:2769E1E05068EB1B9CAF42773B13FA73][OID:0] Retrieving data from data connector failed. Error in importing files. Please check the file to import. Error type: Data Import Error. Fail to load scripts from data connector. Please check whether IServer machine can access the connector's url: https://xxx.com:8443/CommunityConnectors/mstr-native/?proxy=false. Error: unable to verify the first certificate.
Or
2020-09-25 11:35:35.426-04:00 [HOST:biapp][SERVER:CastorServer][PID:1984][THR:7280][Database Classes][Error][UID:B6CD16C240D4A71C4B7C2A8031C6EBE2][SID:2769E1E05068EB1B9CAF42773B13FA73][OID:0] Retrieving data from data connector failed. Error in importing files. Please check the file to import. Error type: Data Import Error. Fail to load scripts from data connector. Please check whether IServer machine can access the connector's url: https://xxx.com:8443/CommunityConnectors/mstr-native/?proxy=false. Error: self signed certificate.
Or
2020-09-25 11:35:35.426-04:00 [HOST:biapp][SERVER:CastorServer][PID:1984][THR:7280][Database Classes][Error][UID:B6CD16C240D4A71C4B7C2A8031C6EBE2][SID:2769E1E05068EB1B9CAF42773B13FA73][OID:0] Retrieving data from data connector failed. Error in importing files. Please check the file to import. Error type: Data Import Error. Fail to load scripts from data connector. Please check whether IServer machine can access the connector's url: https://xxx.com:8443/CommunityConnectors/mstr-native/?proxy=false. Error: unable to get local issuer certificate.
This occurs when the Node.js process tries to verify the certificate in the SSL handshake stage between the Community Connectors server and the Intelligence server. By default, Node.js is built with a bundle of commonly used CA root certificates. However, you may still encounter errors when your Community Connectors server is deployed with self-signed certificates (e.g., a company-specific private CA). Some of these errors include:
Disable the strict SSL by configuring the
JSDisableStrictSSLunder
KEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Strategy\Common Files.
Disabling the strict SSL, as proposed in Solution 1, thoroughly increases the security risk for the system. If you are in the production environment, you are suggested to use this solution.
For the following errors reported by the Node.js process, you should add the extra CA certificates for the Nod.js.
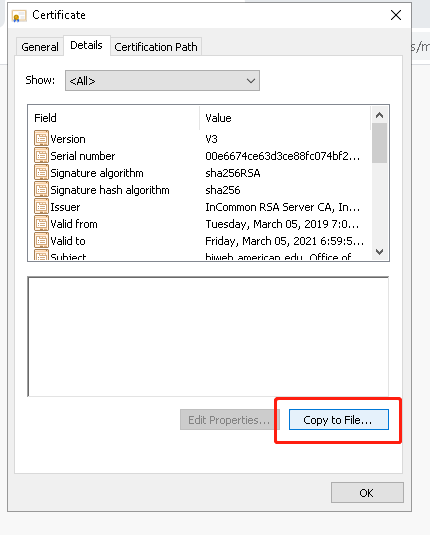
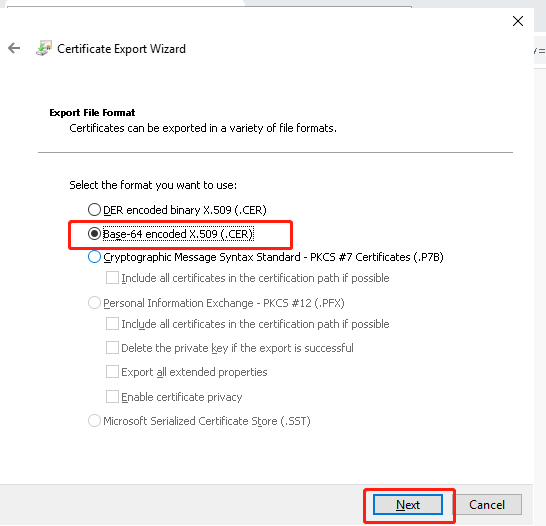
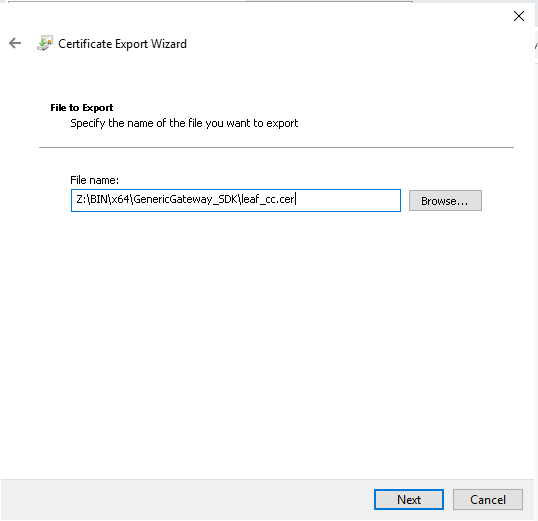
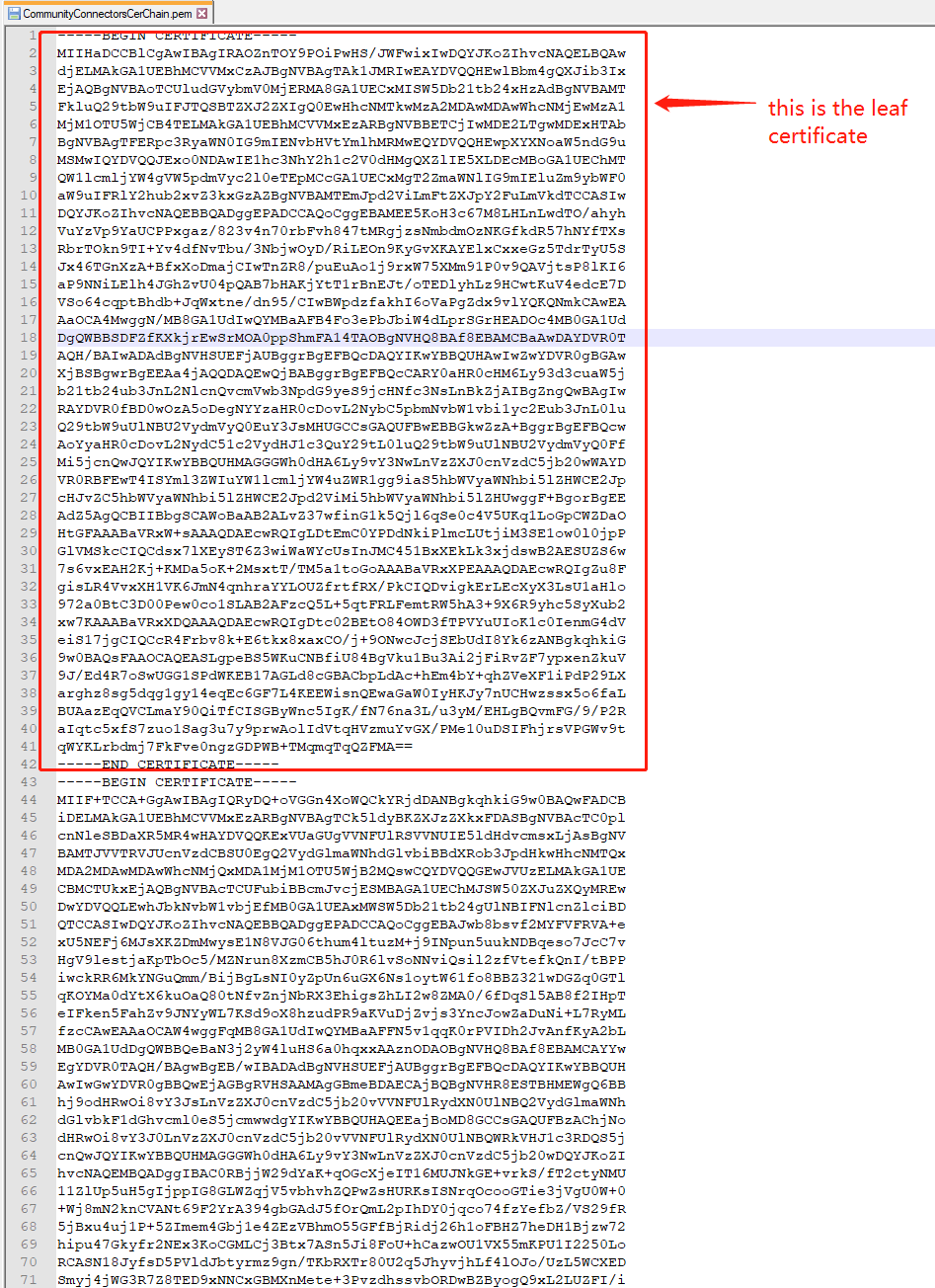
[Intermediate certificate 2 - issued by Intermediate certificate 1] [Intermediate certificate 1 - issued by Root certificate] [Root certificate]
/opt/mstr/MicroStrategy/install.
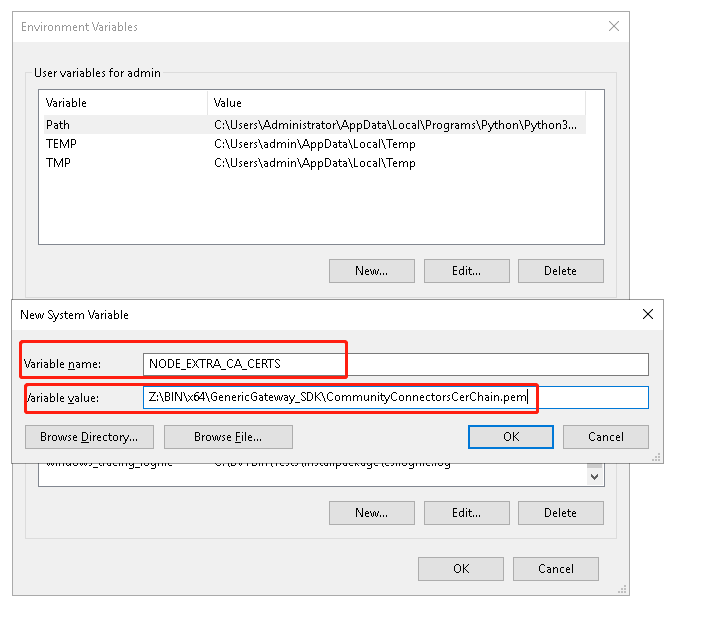
NODE_EXTRA_CA_CERTS="${MSTR_INSTALL_PATH:?}"/CommunityConnectorsCerChain.pem
export NODE_EXTRA_CA_CERTS/opt/mstr/MicroStrategy/env) and grant the execute privilege to the script file. In this folder, there are also many other shell scripts to set environment variables for other purposes, such as ODBC.sh, Registry.sh, JVM32.sh, etc.
#! /bin/ksh
#
# This is the startup script for
# Strategy Control utility
#
# Copyright (c) 2003-2004 Strategy Incorporated
#
. "$(dirname "$0")"/../env/Principal.sh
# . "${MSTR_HOME_PATH:?}"/env/PatchLevel.sh
. "${MSTR_HOME_PATH:?}"/env/BinaryPaths.sh
. "${MSTR_HOME_PATH:?}"/env/Registry.sh
. "${MSTR_HOME_PATH:?}"/env/ODBC.sh
. "${MSTR_HOME_PATH:?}"/env/FontConfiguration.sh
. "${MSTR_HOME_PATH:?}"/env/RIntegrationPack.sh
. "${MSTR_HOME_PATH:?}"/env/Node.sh
exec "${MSTR_INSTALL_PATH:?}"/bin/MSTRCtl "$@"
NODE_EXTRA_CA_CERTS, has taken effect.
[mstr@env-235219laiouse2 bin]$ ps -ef|grep libMSTRSvr mstr 10041 1 20 04:29 ? 00:00:14 /opt/mstr/MicroStrategy/install/bin/MSTRSvr -w /opt/mstr/MicroStrategy/ -t status-iserver.xml /opt/mstr/MicroStrategy/install/lib/libMSTRSvr2.so -n CastorServer [mstr@env-235219laiouse2 bin]$strings /proc/10041/environ |grep NODE_EXTRA_CA_CERTS
NODE_EXTRA_CA_CERTSset.