Starting with the release of Strategy ONE (March 2024), dossiers are also known as dashboards.
Content:
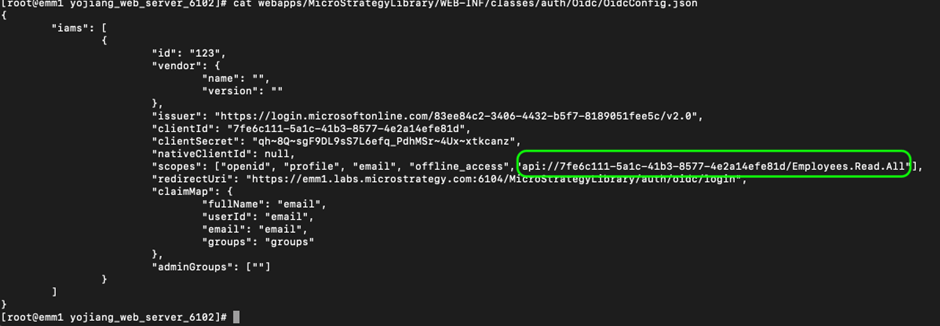
General guidance to configure OIDC authentication for Strategy using Microsoft Azure is provided here: https://www2.microstrategy.com/producthelp/Current/SystemAdmin/WebHelp/Lang_1033/Content/oidc_azure_ad.htm
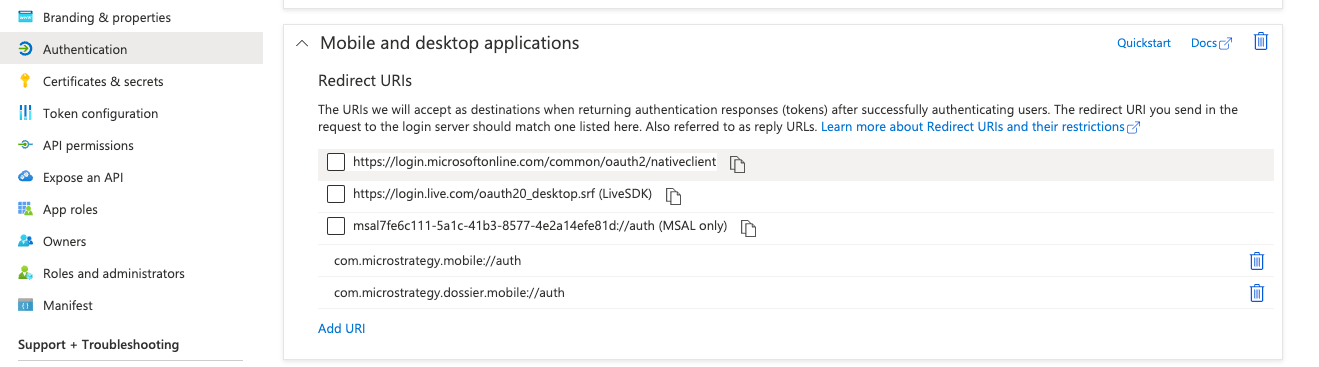
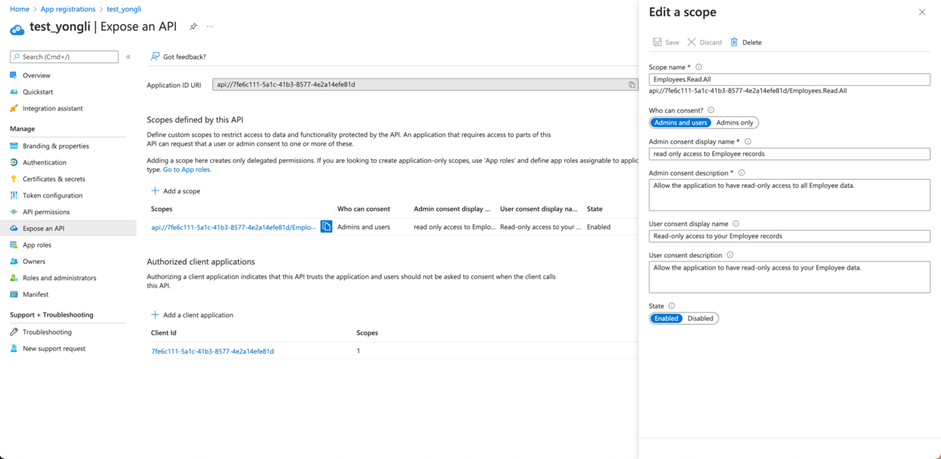
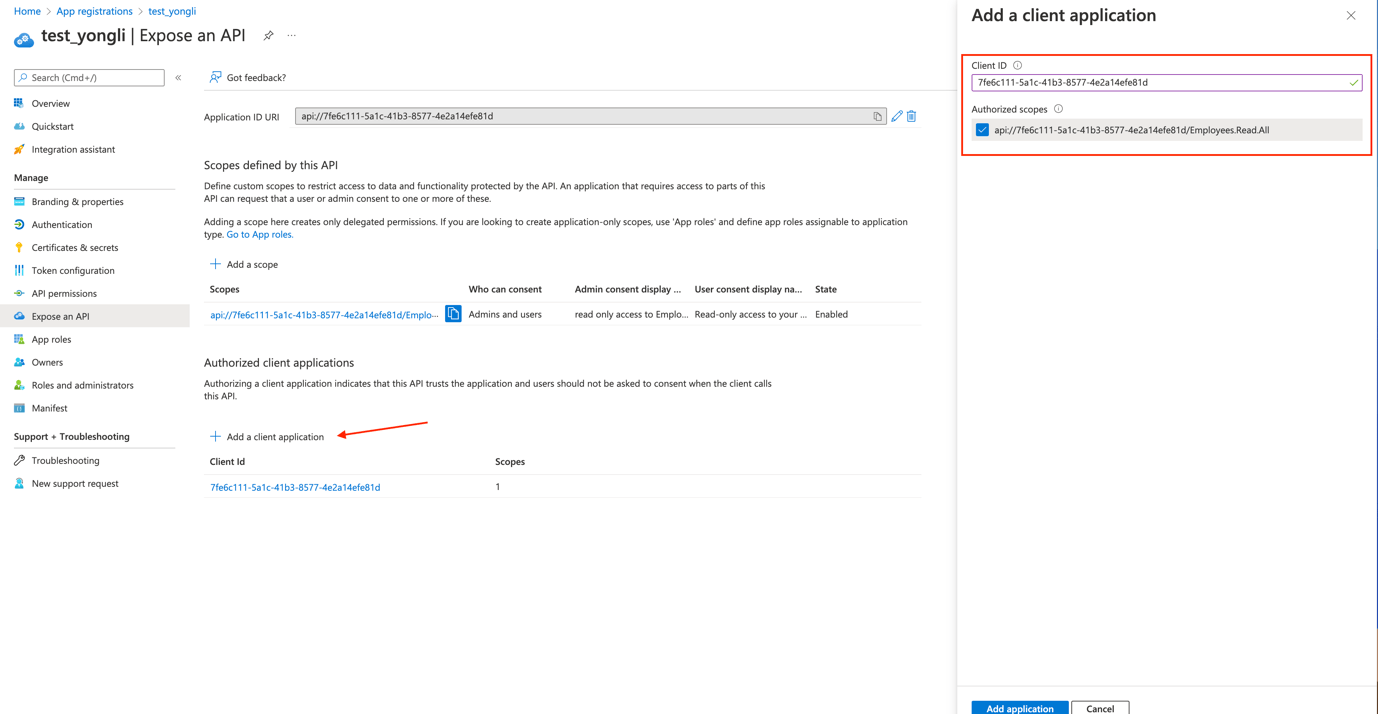
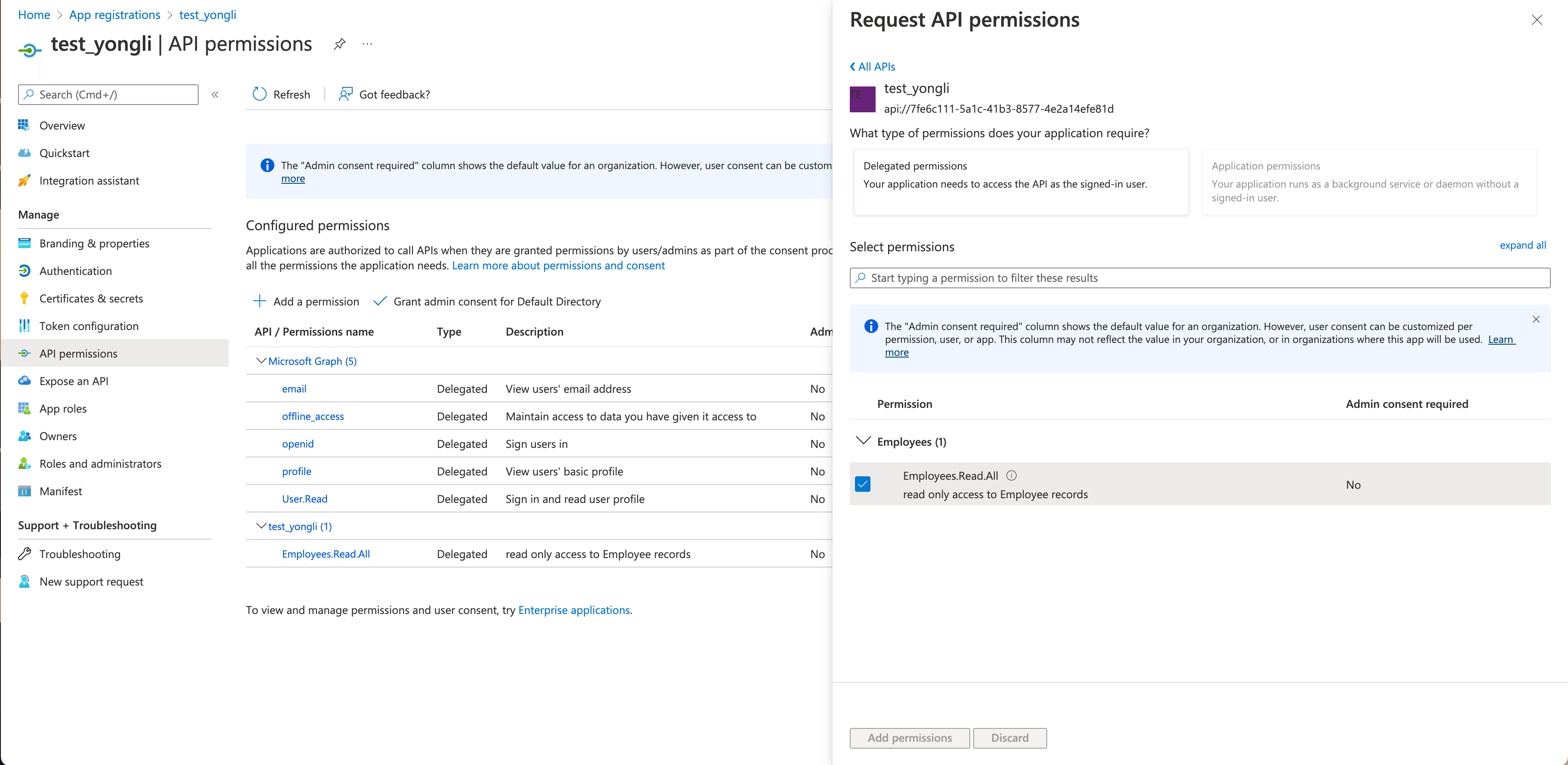
In order to enable Azure multi-factor authentication (MFA) through Azure Conditional Access policies, the following additional steps must be performed for MFA to be triggered when accessing the environment through Strategy Mobile or Strategy Library Mobile:
For steps required to enable MFA through Azure Conditional Access policy, refer to Microsoft documentation.
Third Party Software Installation: WARNING:
The third-party product(s) discussed in this technical note is manufactured by vendors independent of Strategy. Strategy makes no warranty, express, implied or otherwise, regarding this product, including its performance or reliability.