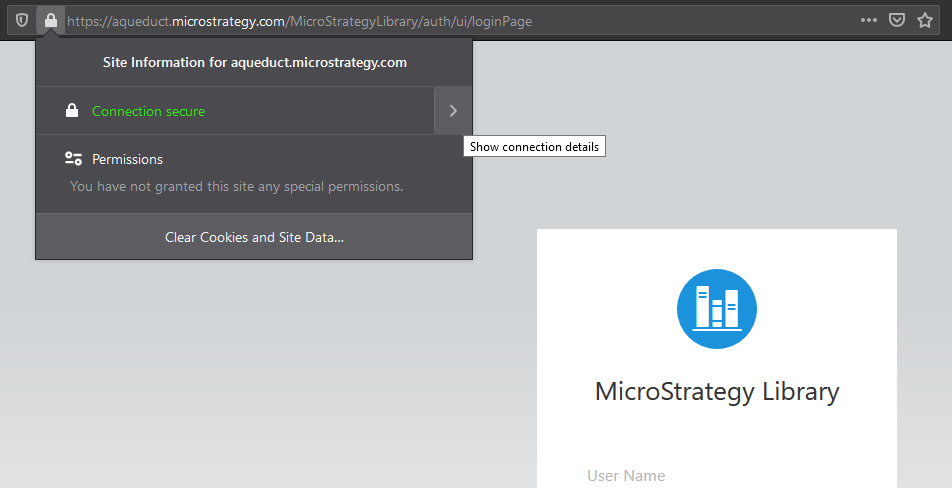
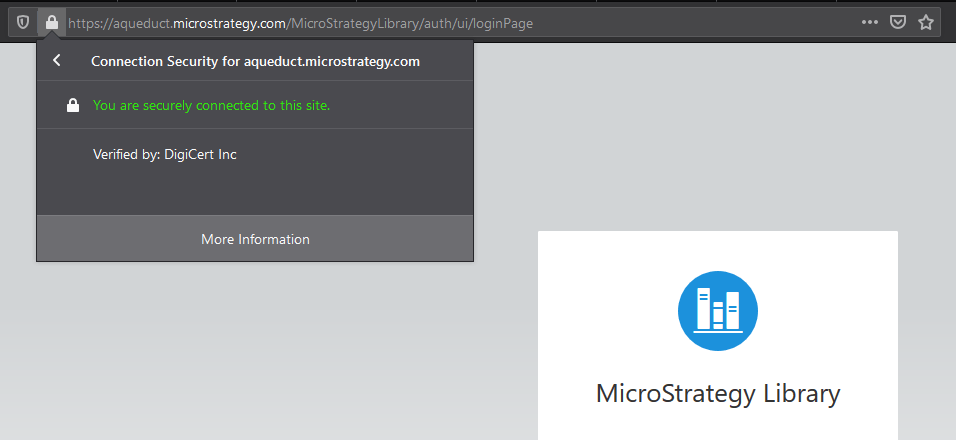
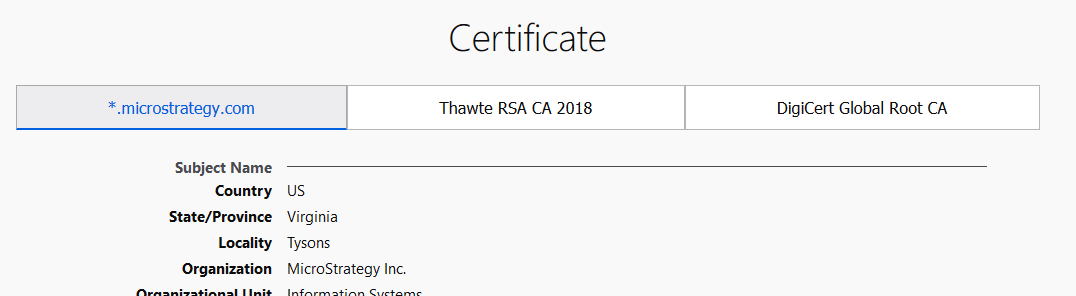
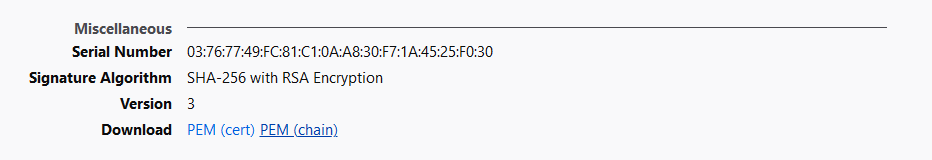
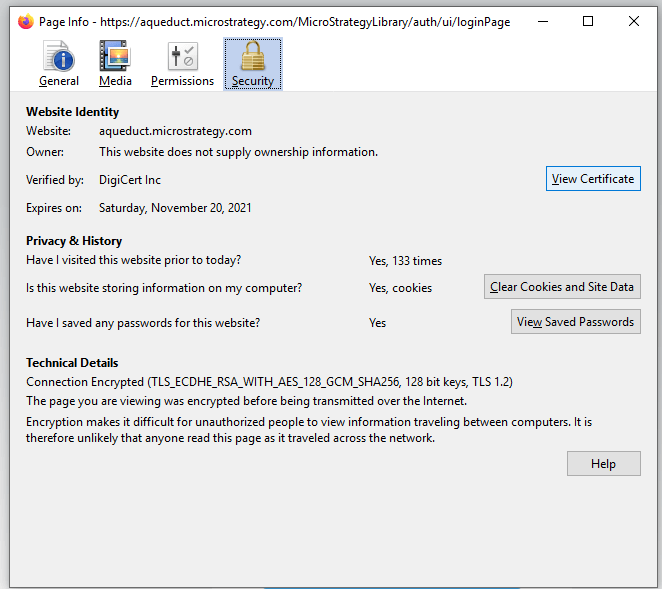
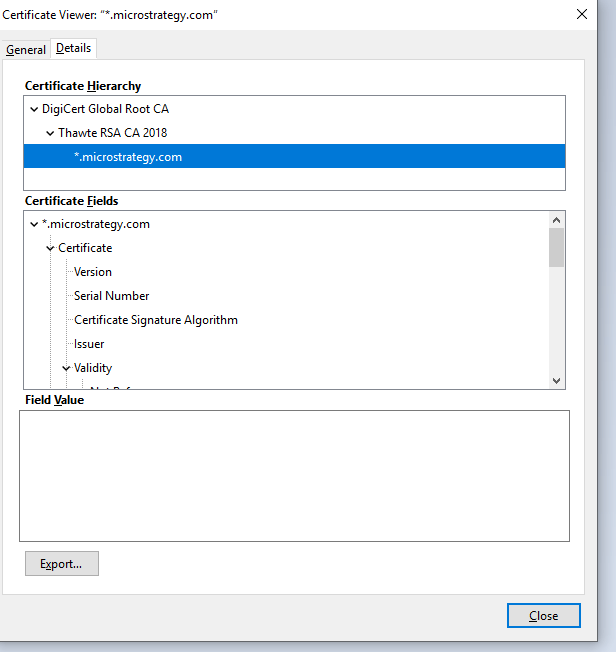
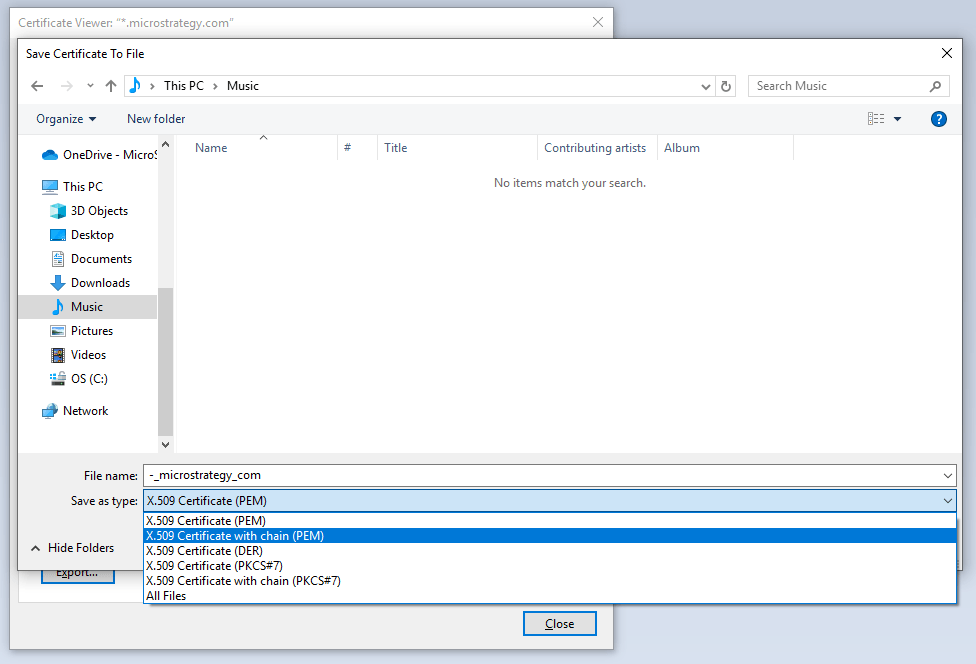
Server certificates can be reviewed from any browser by navigating to the site and viewing the server certificate through the browser. It is highly recommended to use Firefox, which has the explicit download as chain option.
To enable TLS, you need to generate the keystore file for machine hosting the collaboration server. You must have the openssl library installed.
openssl genrsa -des3 -passout pass:mstr123 -out collabsvc.key 2048
openssl req -new -passin pass:mstr123 -key collabsvc.key -out collabsvc.csr
You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [AU]:US State or Province Name (full name) [Some-State]:VA Locality Name (eg, city) []:Tysons Corner Organization Name (eg, company) [Internet Widgits Pty Ltd]:MSTR Organizational Unit Name (eg, section) []:Web Common Name (e.g. server FQDN or YOUR name) []:mac-qfan Email Address []:qfan@Strategy.com Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []:mstr123 An optional company name []:Strategy
openssl x509 -req -passin pass:mstr123 -days 1024 -in collabsvc.csr -signkey collabsvc.key -out collabsvc.crt
openssl pkcs12 -export -in collabsvc.crt -inkey collabsvc.key -out collabsvc.pfx