For SAML setup info on MSTR side refer to our documentation.
Create new Okta custom app
Note that only an Okta administrator can create and configure custom apps.
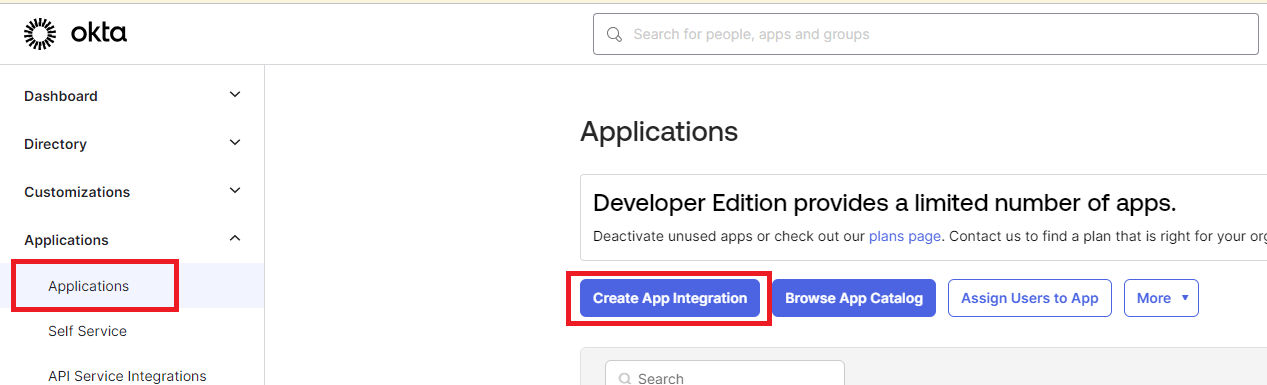
Log in to Okta Administrator Dashboard and go to the "Applications" link on the left-side navigation bar. Then, Select "Create App Integration"
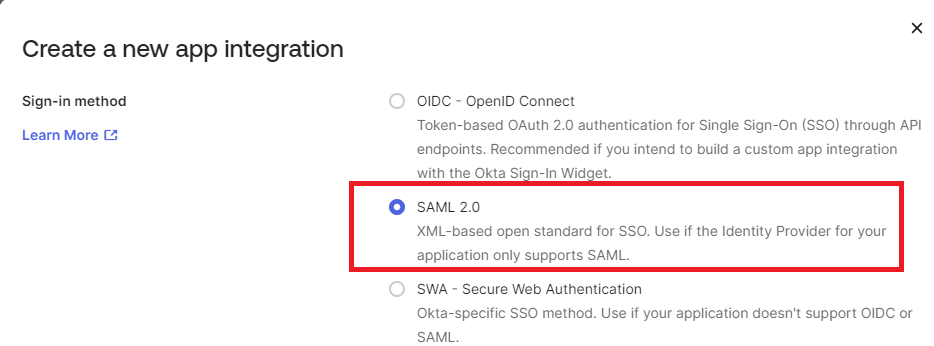
Select "SAML 2.0" as the sign on method, then click "Next"
The Create SAML Integration page will then show up.
Finish step 1 "General Settings" (application name, icon, etc.) as desired.
Okta app SAML configuration
Note: it's recommended to finish SAML setup on the Strategy side first so that values can be directly copied over from the generated configuration files.
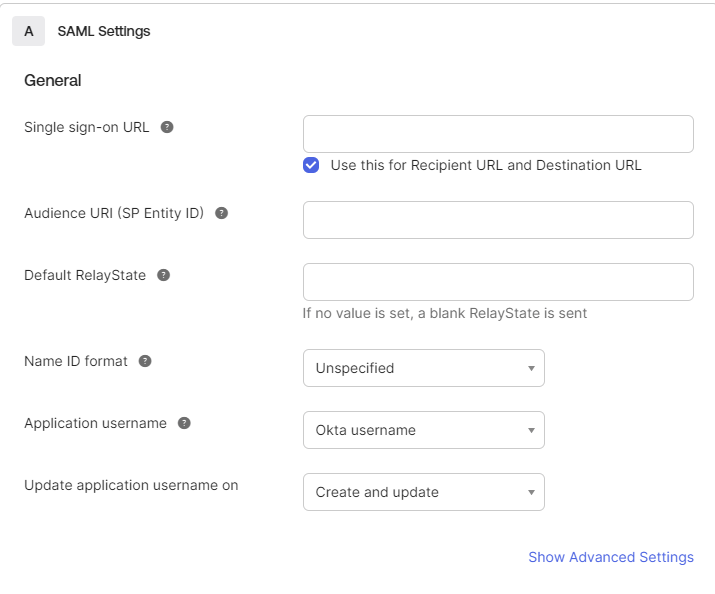
In Step 2, SAML options will show as follows:
"Show advanced settings" will drop down additional SAML settings:
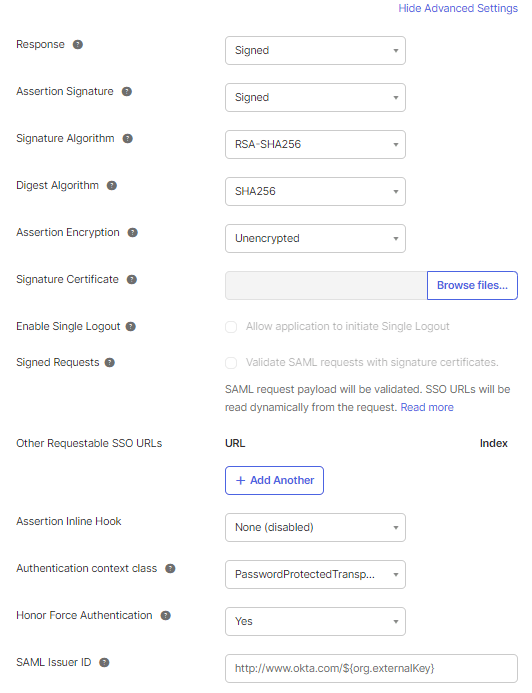
Some notes on the advanced settings:
Configure attribute mapping
The last part of SAML configuration attributes mapping:
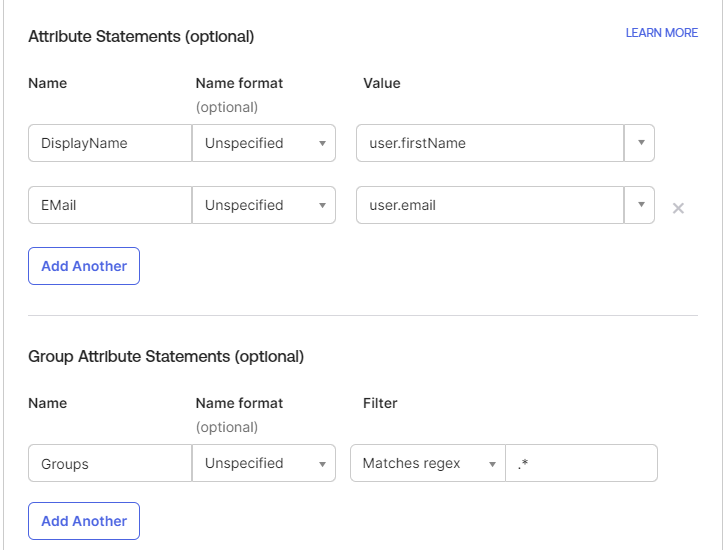
This is to configure what SAML attributes to be sent to Strategy. Currently, Strategy is asking for four attributes that could potentially be used inside Strategy, namely "Email", "DistinguishedName", "DisplayName" and "Groups" if default names were used at Strategy SAML configuration. The attribute name mapping can also be found in the MstrSamlConfig.xml file.
Detailed information about attribute mapping can be found in the document for Strategy SAML configuration, but generally, it's not required to send over all these attributes. Authentication should work even if no attribute is sent. However, the "Groups" information is more important since the information is used to grant access to the Strategy Web/Mobile admin page, and it can also be used to further integrate into Strategy groups to do user privilege management. Configure what value is to be sent in the attributes (or not sending anything at all) as needed.
Note on group attribute setting: Okta placed a configurable filter for sending out group information in case too many unused groups are sent over. The filters can be set to send over all groups that a user belongs to. For this functionality, the filter needs to be set as "Regex", with .’*’ as shown in the screenshot above.
After defining the attributes, click "Next" Under the 'Preview the SAML Assertion' section.
Then click "Finish."
Finish SAML setup
The next page should be the "Sign On" tab for the newly created Okta Application:
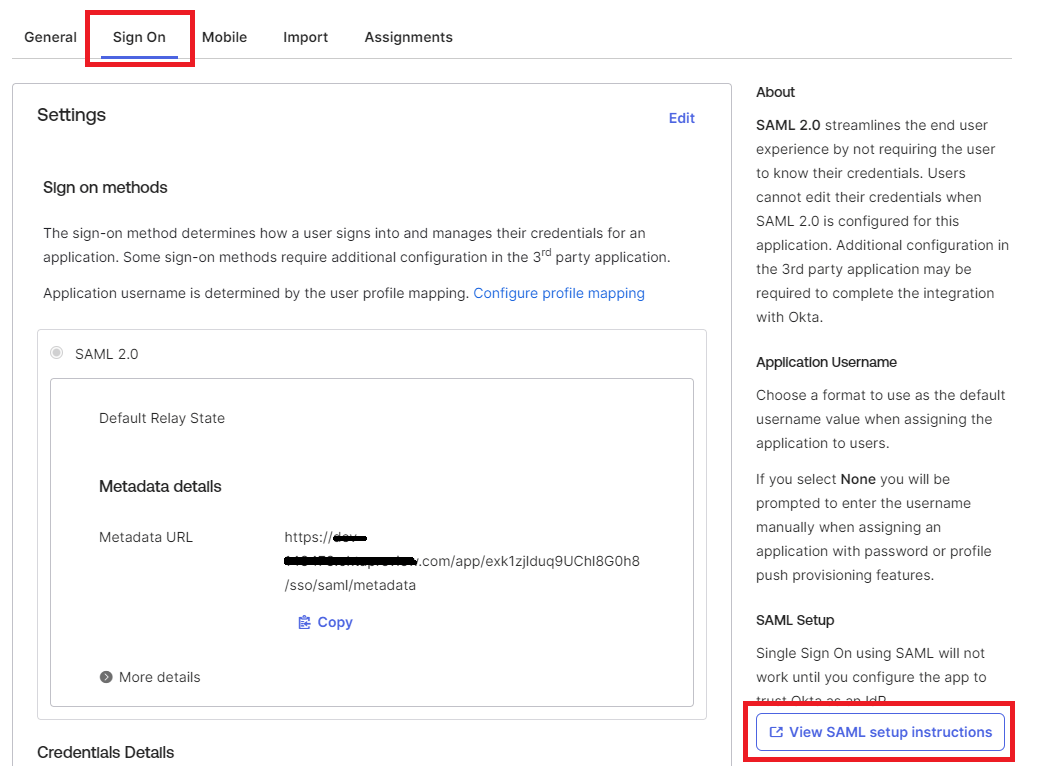
On the right side of the page, select the "View SAML setup instructions" button to retrieve the application metadata.
Copy the XML content from the "Optional" section at the bottom of the page and save it to a file named "IDPMetadata.xml.
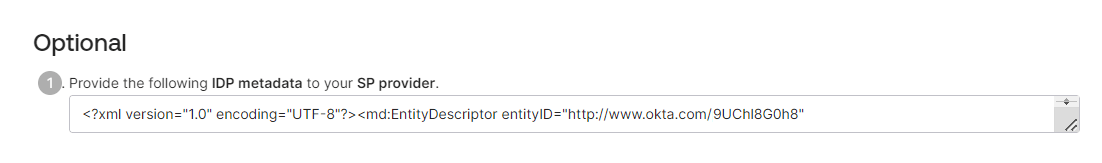
Copy this newly created IDPMetadata.xml file to the /SAML folder in the Web application.
Web: /MicroStrategy/WEB-INF/classes/resources/SAML
Library: /StrategyLibrary/WEB-INF/classes/auth/SAML
Final Note
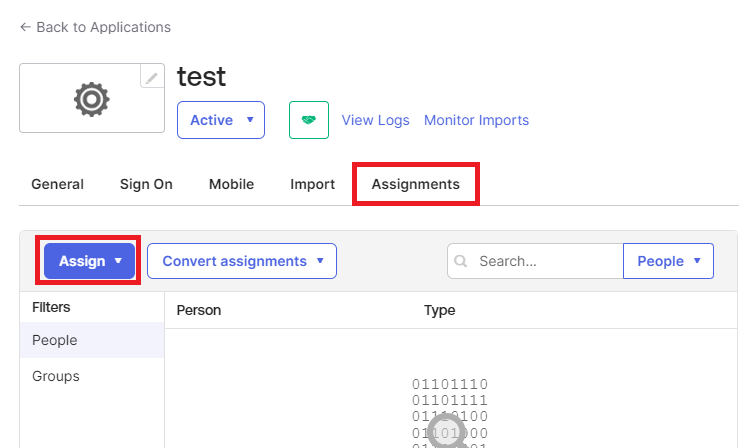
Ensure that the users and groups in Okta are assigned to the application that was created by navigating to the "Assignments" tab, then clicking "Assign" and selecting the Users/Groups to be assigned to this application.
Third Party Software Installation: WARNING:
The third-party product(s) discussed in this technical note is manufactured by vendors independent of Strategy. Strategy makes no warranty, express, implied or otherwise, regarding this product, including its performance or reliability.
KB440543