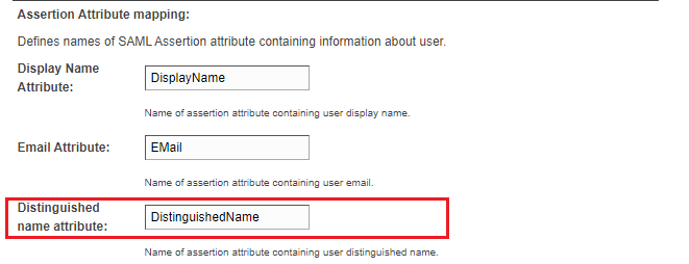
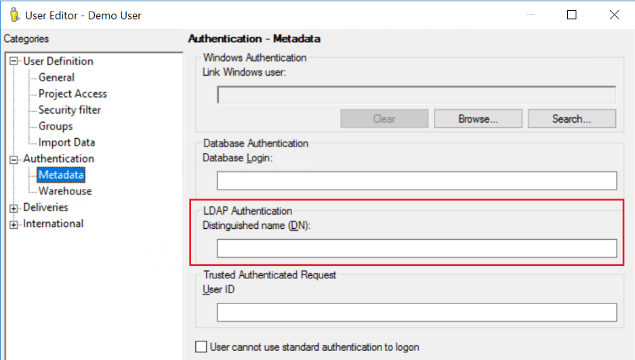
Distinguished name attribute can be used to link SAML users to Strategy users.
The Admin Groups field in the SAML Configuration page is for access control of the Strategy Web/Mobile Administrator page. A user is able to access the Strategy Web/Mobile Administrator page if he or she belongs to the admin groups that are predefined in the SAML Configuration page. Otherwise, a 403 error is displayed.
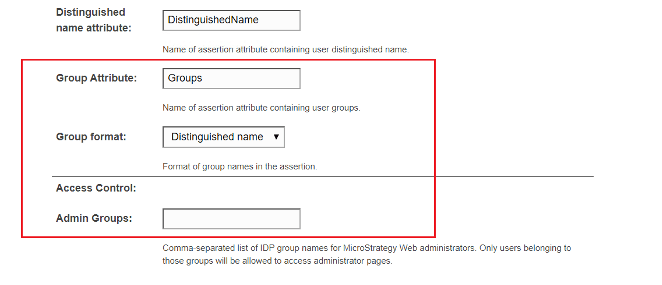
To utilize LDAP integration with SAML, Group format can be set to Distinguished name. In the Admin Groups field, enter the value of the CN field of the user’s group DN.
For example, in a SAML response, a user has a SAML attribute called “Groups” and its value is “CN=mstrAdmin, ou=Groups, dc=edu," as shown below:
<saml2:Attribute Name="Groups " NameFormat="urn:oasis:names:tc:SAML:2.0:attrname-format:unspecified">
<saml2:AttributeValue xmlns:xs="http://www.w3.org/2001/XMLSchema" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:type="xs:string">CN=mstrAdmin,ou=Groups, dc=edu</saml2:AttributeValue>
</saml2:Attribute>
In the Admin Groups field, enter mstrAdmin.
Note: