In order to set up LDAP authentication using either Clear text or SSL on Strategy Intelligence Server Universal 9.x-10.x on Linux the following steps need to be performed:
SSL Connection
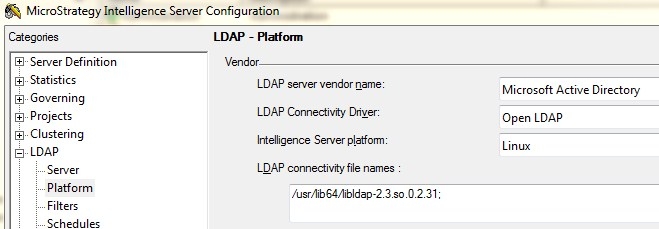
With the Strategy Intelligence Server 9.x-10.x, users only need the Certification Authority (CA) certificate for the CA used to sign the LDAP Server SSL certificate. This certificate should be placed in a folder accessible to the Intelligence Server and must be named "cacert.pem" and must be in the Base64 encoded pem format. The folder containing the file must be specified in the Intelligence Server LDAP configuration as shown in the screenshot below.

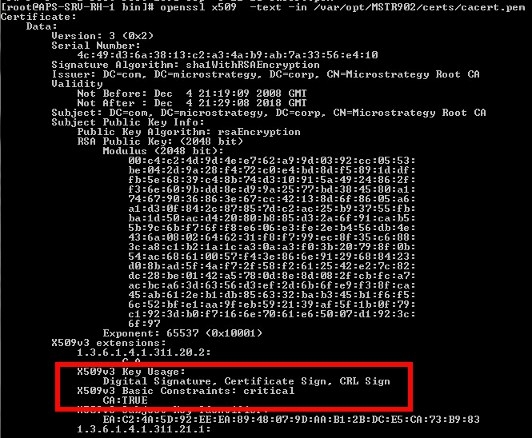
Configure the LDAP certificate setting in the Strategy Intelligence Server Definition through Strategy Desktop or Control Center by typing in the full path to the certificate files as shown in the screenshot above. The user can use openssl commands to check the validity of the CA certificate as shown below: