This document provides steps to setup single sign-on access to Vertica (using Kerberos) when Strategy Intelligence Server 9.4.1 or 10.x resides on a Windows operating system.
Create user on Active Directory and assign the SPN
ktpass -princ <SPN> -mapuser <AD User> -mapop set -pass <pw> -crypto rc4-hmac-nt -ptype KRB5_NT_SRV_HST -out <c:\path\file> IE: ktpass -princ host/tsvertica71.labs.Strategy.com@LABS.Strategy.COM -mapuser verticakerb -mapop set -pass <pw> -crypto rc4-hmac-nt -ptype KRB5_NT_SRV_HST -out c:\vertica.keytab
Setup Single Sign-On (SSO) with Vertica
KerberosHostname:
SELECT set_config_parameter('KerberosHostname', '<host_name>');
Example:
SELECT set_config_parameter('KerberosHostname', 'ts-vertica89.labs.Strategy.com');
KerberosKeytabFile:
SELECT set_config_parameter('KerberosKeytabFile', '/<location>/<keytab_file>');
Example:
SELECT set_config_parameter('KerberosKeytabFile', '/vertica/db_1/v_node0001_catalog/vertica.keytab');
KeberosRealm:
SELECT set_config_parameter('KeberosRealm', '<KerberosRealm>');
Example:
SELECT set_config_parameter('KeberosRealm', 'LABS.Strategy.COM');
KeberosServiceName:
SELECT set_config_parameter('KeberosServiceName', '<kerberos_service_name>');
Example:
SELECT set_config_parameter('KeberosServiceName', 'vertica');CREATE AUTHENTICATION <auth_name> METHOD 'gss' HOST '0.0.0.0/0';
ALTER AUTHENTICATION <auth_name> ENABLE;
CREATE USER <AD_user> identified by '<password>';
GRANT AUTHENTICATION <auth_name> to <AD_user>;
Confirm that SSO is working
vsql -k <KeberosServiceName> -K <KerberosHostname> -h <db_host> -U <AD_user> Example: vsql -k vertica -K ts-vertica71.labs.Strategy.com -h ts-vertica71.labs.Strategy.com -U verticakerb
CREATE AUTHENTICATION <auth_name> METHOD 'password' HOST '0.0.0.0/0';
GRANT AUTHENTICATION <auth_name> to <db_user>;
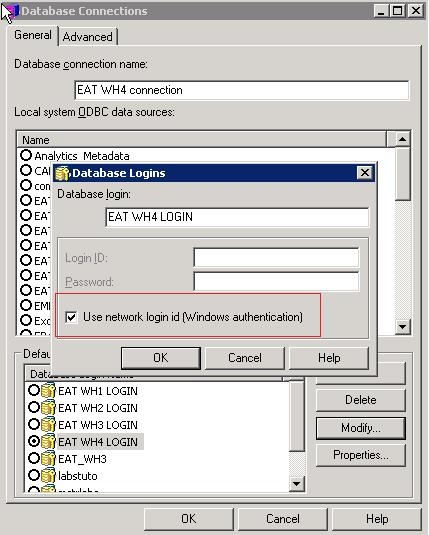
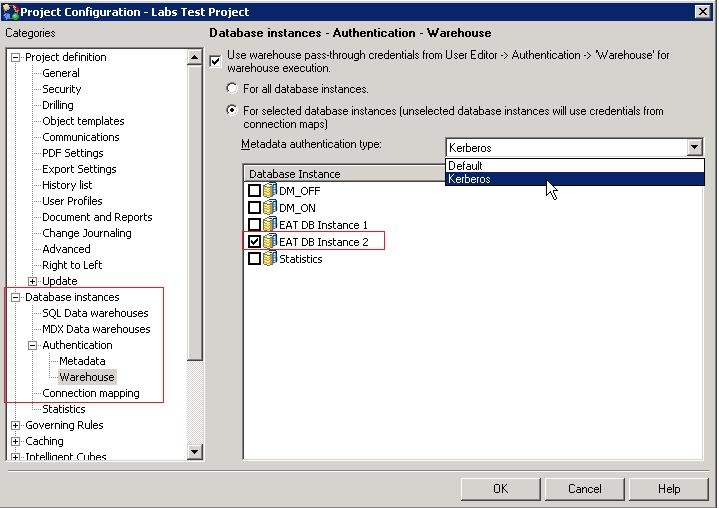
Setting up Strategy
<PROPERTY NAME="SupportsKerberos" VALUE="1"/>