SUMMARY
Entropy is often overlooked, misconfigured or forgotten and it can originate in sporadic errors whether it can be timeouts, refused connections, etc. that, for example, could affect the SSL communication used by Strategy Products. Such errors are difficult to debug as the errors happen only when there is not enough entropy available.
Note:
This article is meant to provide some helpful hints about entropy. It is not meant to be exhaustive or definitive. There are hundreds of information sources on the Internet.
Many processes generate certificates, keys, IDs, etc., so they need a random source to avoid generating those assets in a predictable way. In RedHat and other Linux distributions there are a couple of special devices that can be used for gathering random numbers for those processes:
/dev/random /dev/urandom
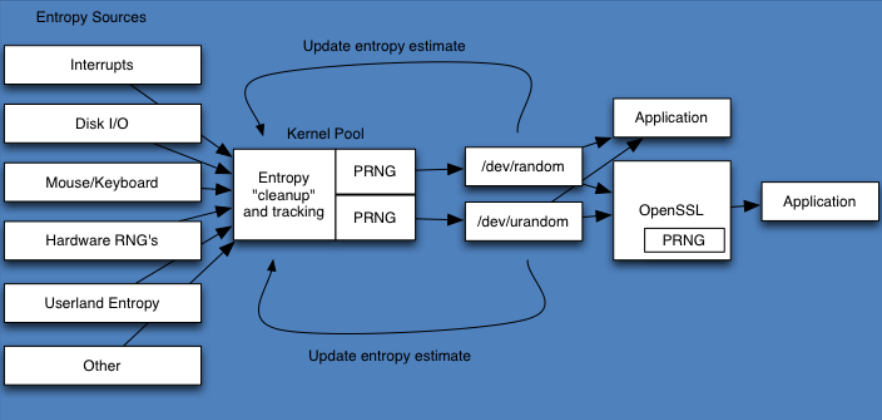
Source: BlackHat 2015
Essential points:
-Entropy is the uncertainty of an outcome.
-Randomness is about the quality of that uncertainty from a historical perspective.
-Full entropy is 100% random.
-Entropy has a quantity.
-Randomness has a quality.
SYMPTOM
Errors like the following can be seen recorded at the DSSErrors.log file:
[Database Classes][Error] Connect failed. Unable to connect. Error communicating with connection process. Child Process hung: Command ConnectionConnectWithNewParameters. It may be stressed. Error type: System call error. Error communicating with connection process. Child Process hung: Command ConnectionConnectWithNewParameters. The target data source hasn't responded to the Connect request after 300 seconds. It may be stressed. Connection String: DSN=DSN_NAME;UID=mstradmin;. SQL Statement: Connect. [MultiProcess][Error] Cannot execute command because there was an error on a previous command 2018-09-26 11:05:30.311-05:00 [HOST:vxpip-pmstri02][SERVER:CastorServer][PID:57585][THR:705828608][Metadata Server][Error][0x80041404] Database error <1>: Connect failed. Unable to connect.
cat /proc/sys/kernel/random/entropy_avail
ln -sf /dev/urandom /dev/random
rngd -r /dev/urandom