This article takes a deep dive into the OIDC authentication flow and configurations supported by Strategy. This can be helpful if you are using a custom identity provider and want to integrate it with MicroStrategy OIDC authentication.
OpenID Connect is an identity protocol and open standard that is built on OAuth 2.0 protocol. It enables applications such as Strategy, the relying party (RP), to rely on authentication that is performed by an OpenID Connect Provider (OP) to verify the identity of a user. Upon the successful authentication and generation of an access token, Strategy requests basic user information from the identity provider to create a user in the Strategy metadata.
Strategy supports the Client Authorization Code + Client Secret key flow and the Client Authorization Code + PKCE (supports native applications) flow. If the same Strategy application needs to be accessed by both web clients (browsers) and native applications (Desktop and Mobile apps) it is possible to configure the application to use both workflows. Strategy does not support implicit flow, as it is not recommended by the OAuth 2.0 working group.
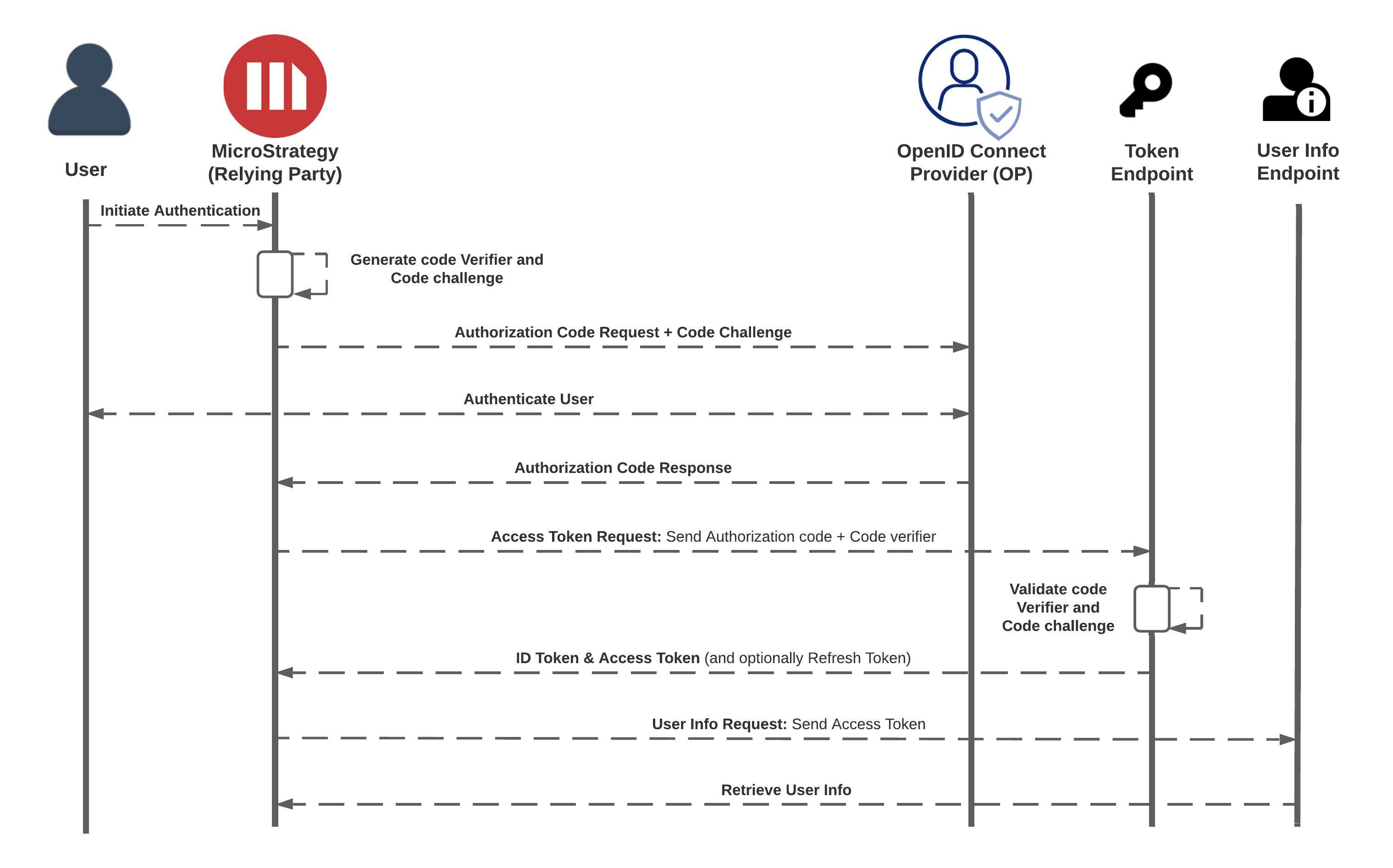
The Client Authorization Code + PKCE (supports native applications) flow is recommended as it supports all Strategy clients. In this flow, Strategy does not need the client secret key and generates a hashed code challenge instead.
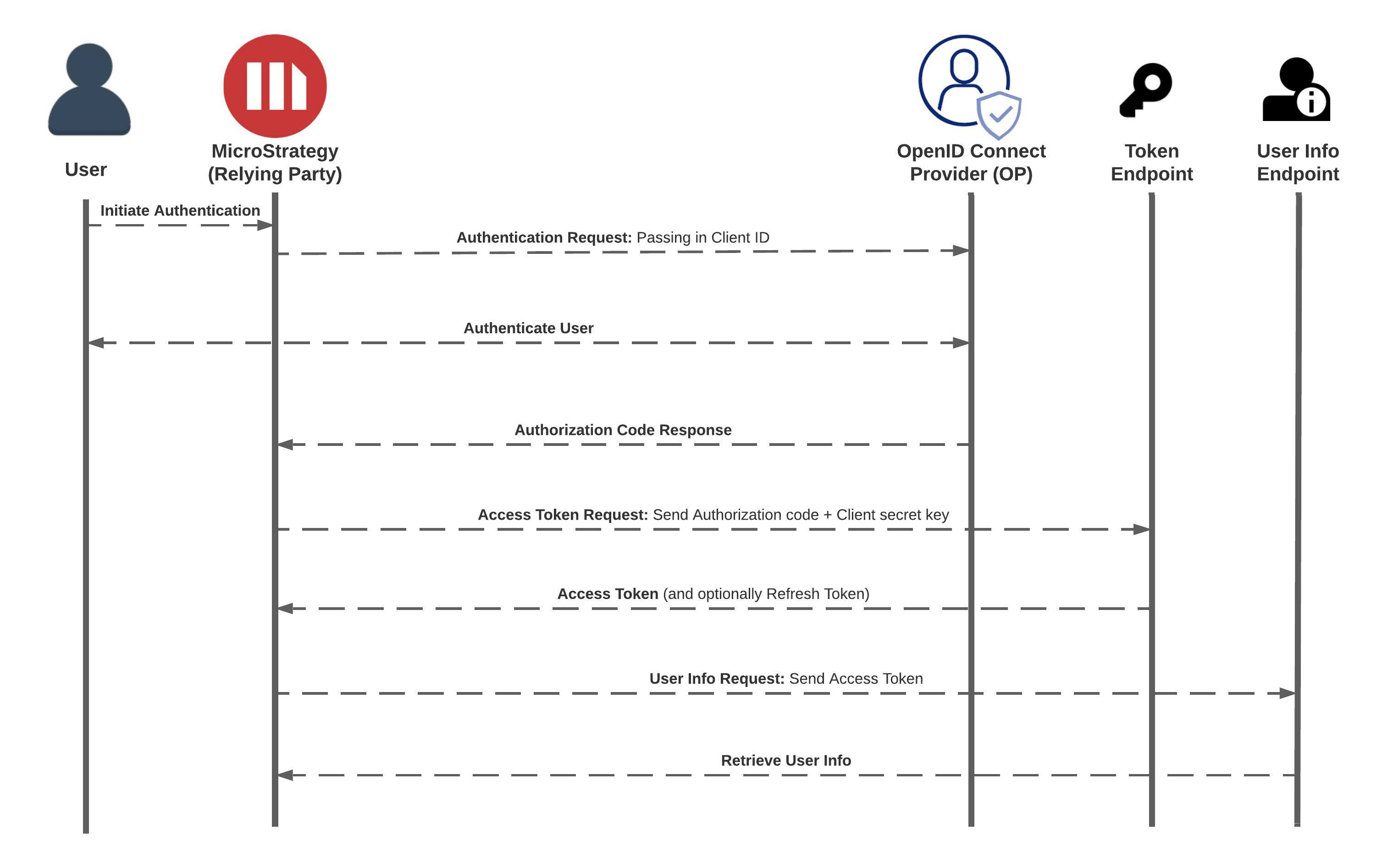
The Client Authorization Code + Client Secret key flow is supported by Web and Library Web only. It is not supported by native applications such as Workstation and mobile apps. In this flow, Strategy must have the client secret key to complete the authentication.
name,
family_name,
given_name,
middle_name,
nickname,
preferred_username,
profile,
picture,
website,
gender,
birthdate,
zoneinfo,
locale, and
updated_at.