Starting with the release of Strategy ONE (March 2024), dossiers are also known as dashboards.
Starting with the release of Strategy 2019 and later versions, certain customers have informed Strategy about incorrect Out of Compliance messages for their environments. After internal investigation, it was found that this is related to having both a Named User and CPU License Key for the same Intelligence server cluster, referred to as a Mixed Named User CPU License Key.
By default, License Manager automatically performs compliance checks and provides information about the compliance status to System Administrators. To eliminate false positive messages from License Manager, compliance checks for Mixed Named User CPU deployments are temporarily suspended in Strategy Secure Enterprise 2019 Update 2 (11.1.2) while Strategy’s Technology Team is works on system improvements.
This article provides general steps for manually checking compliance of a mixed deployment to assist Strategy Administrators in maintaining their environments. If you have any questions about these changes or need assistance manually checking compliance, please contact your Account Executive.
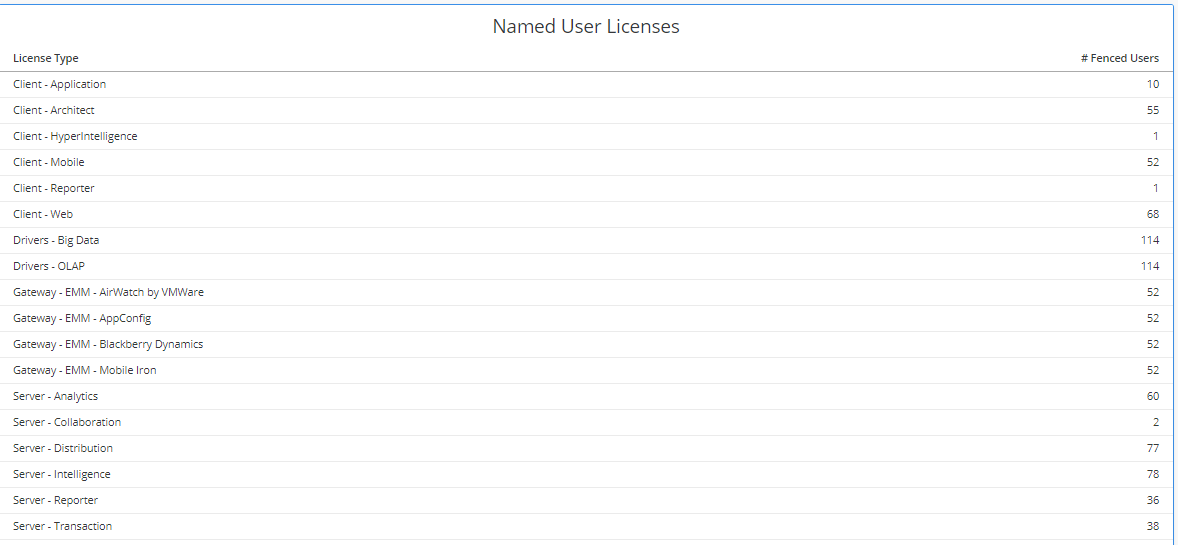
Deploying an environment using both a CPU and Named User License in a clustered Intelligence server varies from situation to situation. The most common method of setting up this type of environment is using User Fencing to dictate the Named User License profiles to a single node and then using the CPU License for the remaining unfenced users. This method restricts the traditionally higher functionality or higher priority Users to a system that can utilize all the available hardware, while the bulk of Users would be sharing the hardware limited machines.
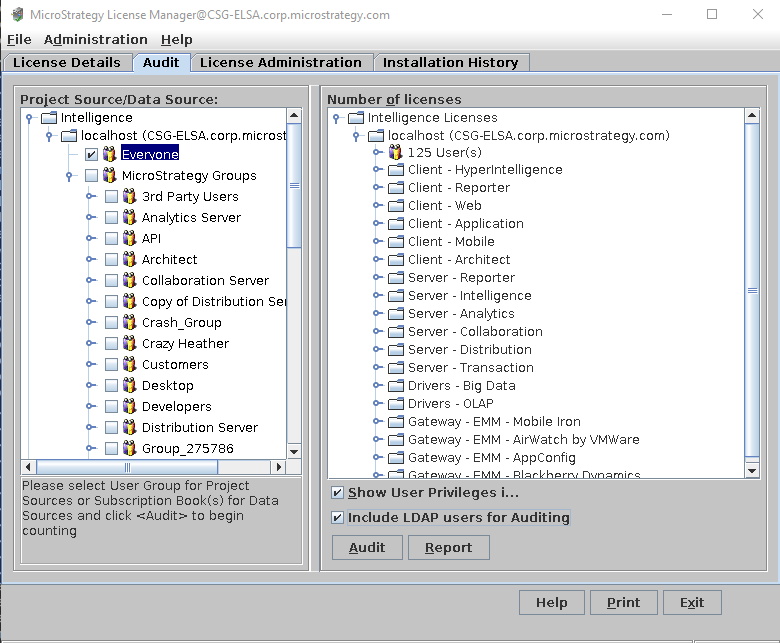
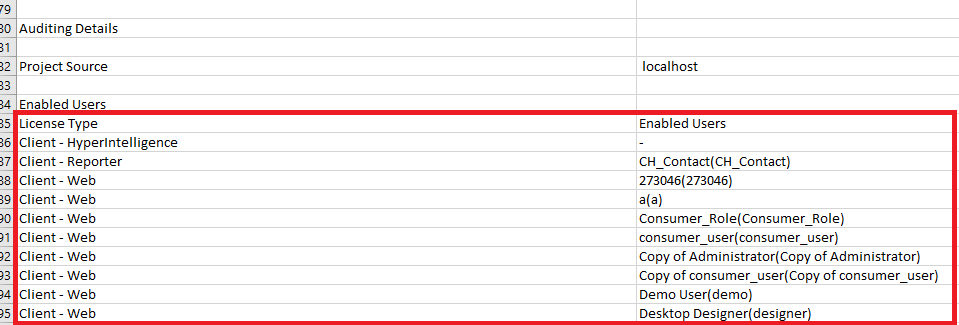
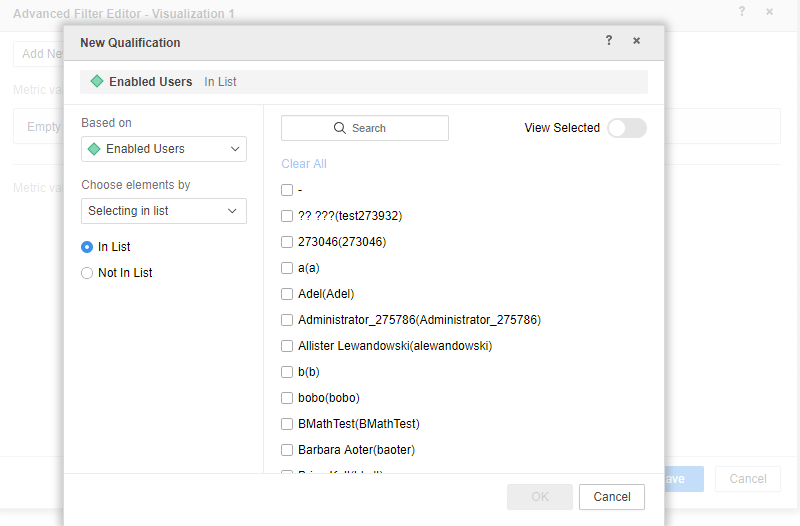
For the purpose of running a Manual Compliance Check, it's best to have a single User Group containing all Users who will be fenced to the Named User Licensed Intelligence server node. This allows for quick identification of fenced Users and a faster analysis of the Named User compliance.
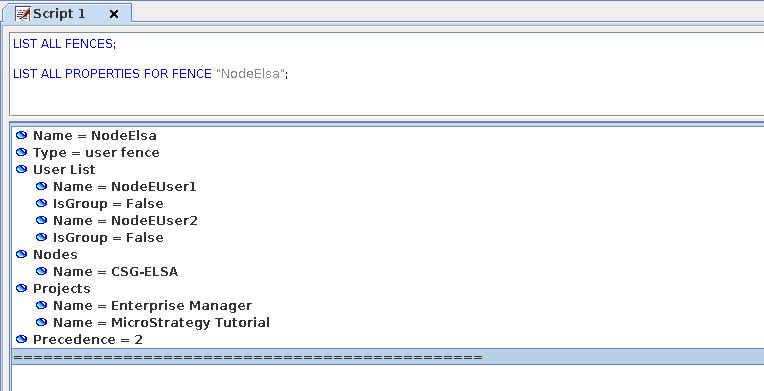
LIST ALL FENCES; LIST ALL PROPERTIES FOR FENCE “<user-fence>”
Count<Distinct=True>([Enabled Users]@ID){~+}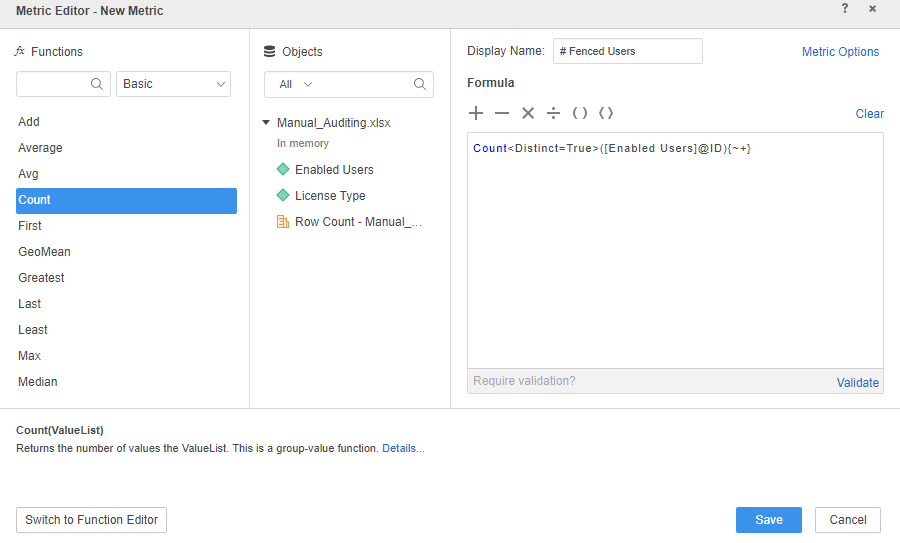
To check the CPU compliance in a mixed deployment, you can use Service Manager or MSIReg.reg.
The CPU compliance of an environment is based on the total number of processors utilized by the Strategy Secure Enterprise for the same DSI and Key Group. This means that for a Mixed Named User CPU deployment, each Intelligence server using the CPU portion of the license in the same subnet needs to aggregate the number of processors.
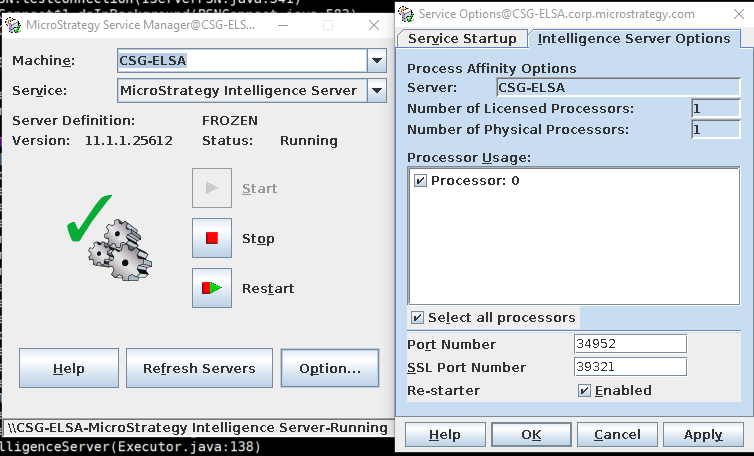
You can find the same information from Service Manager using MSIReg.reg.
[HKEY_LOCAL_MACHINE\SOFTWARE\Strategy\DSS Server\Castor].
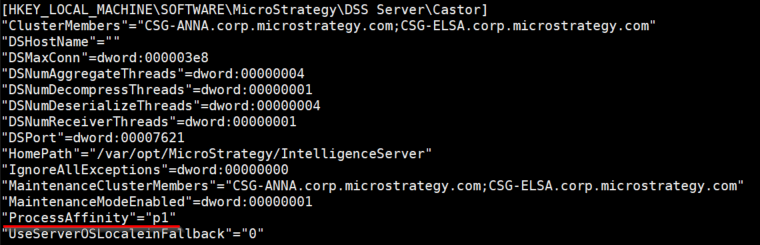
ProcessAffinityis followed by a
pand any number of
0's and
1's. Each
1present inside the mask represents a processor selected for affinity. Each
0is a restricted processor. The mask does not need to have the number of digits equal to the total number of processors on the Intelligence server. If there are less than the number of processors on the I-server, it will begin counting from
processor 0onward.
When performing a Manual Compliance Audit, if you find your environment is out of compliance or you have questions, please contact your Account Team. If your environment is out of compliance, they can discuss methods of bringing the environment back into compliance.