Snowflake has posted details on how to secure connections to Snowflake.
This includes two steps Strategy customers who use Snowflake should take:
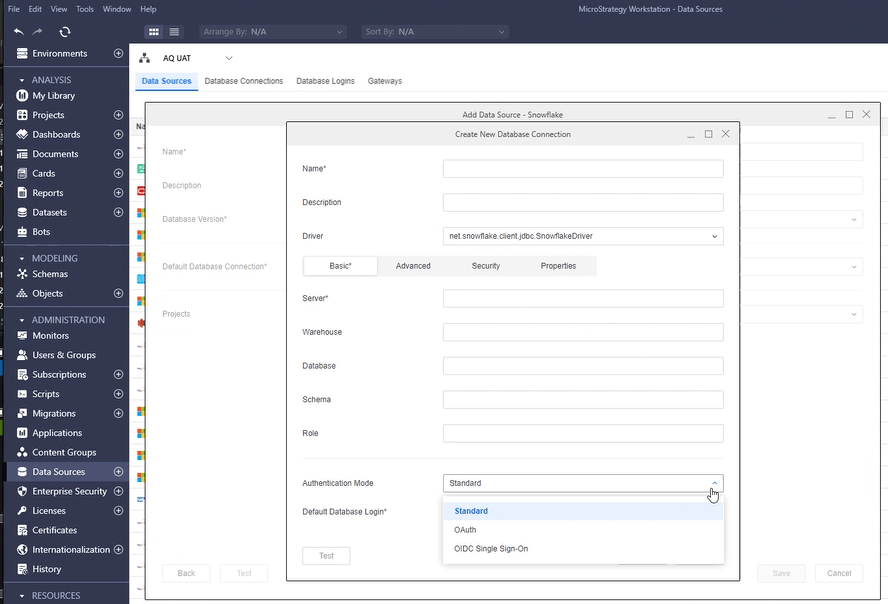
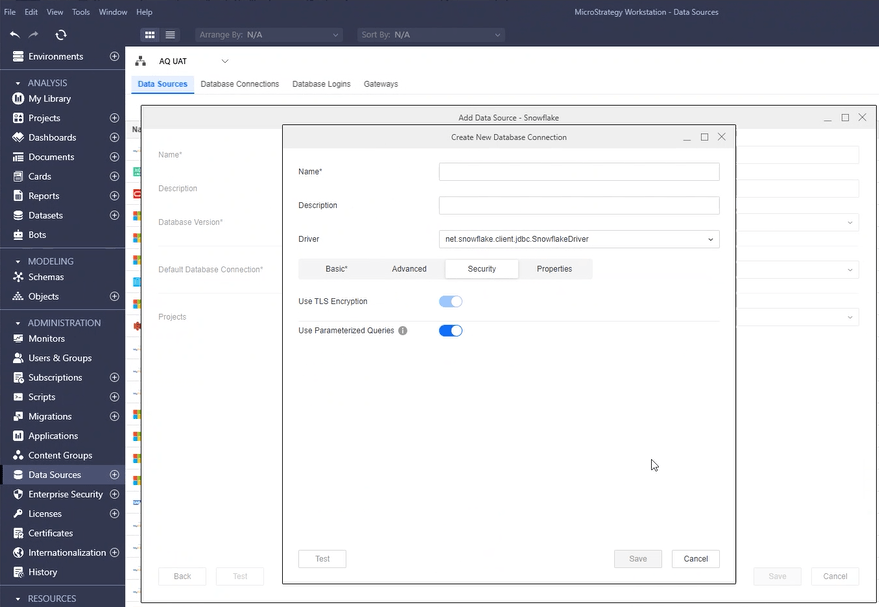
Strategy Customers utilizing Snowflake can perform the following actions to ensure the Strategy configuration of Snowflake follows security best practices:
In summary, Strategy recommends:
Strategy recommends source restrictions as a general best practice. Users of Strategy Cloud can open a Strategy Technical Support Case for assistance in identifying source IP address ranges.