After configuring and testing a Strategy on AWS Trial environment, there are four main steps to further configure the environment to a full production environment.
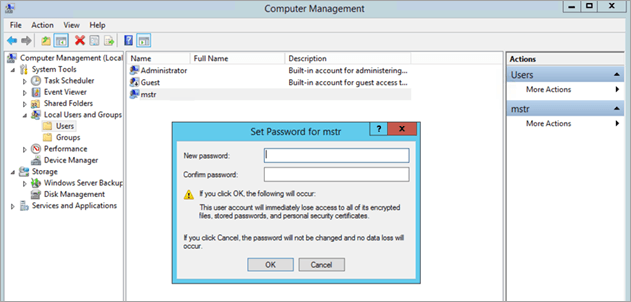
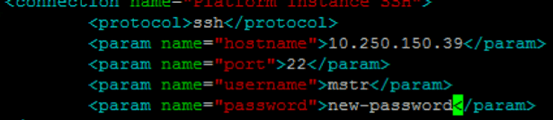
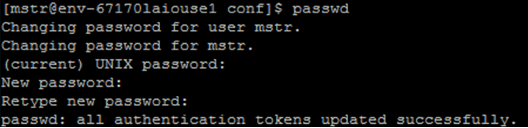
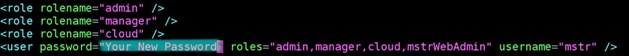
Change the default passwords for:
service mstr tomcatrestart.
opt/mstr/MicroStrategy/install/Repository/bin/mstr_psql -d poc_metadata -h HOSTNAME -U mstr
For steps to change another user's password, see How to Change a User's Password .
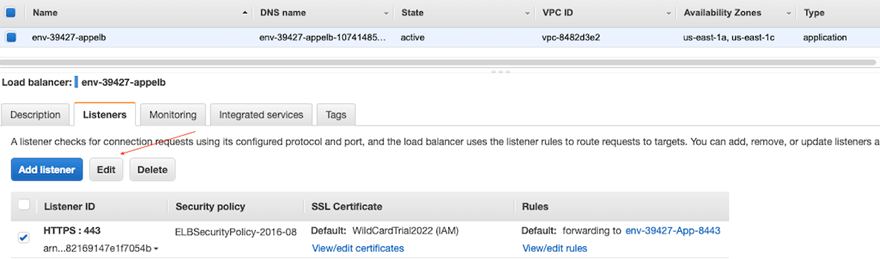
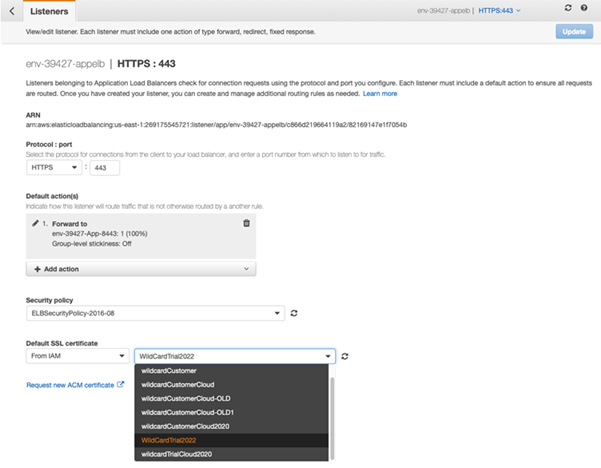
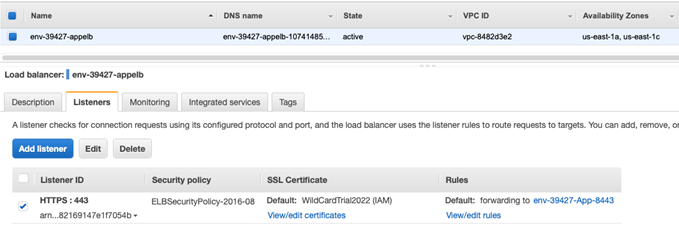
Add certificates to the AWS Account: