After logging into Strategy Library 2021 Update 4 using HTTP, users may get the following error on the page:
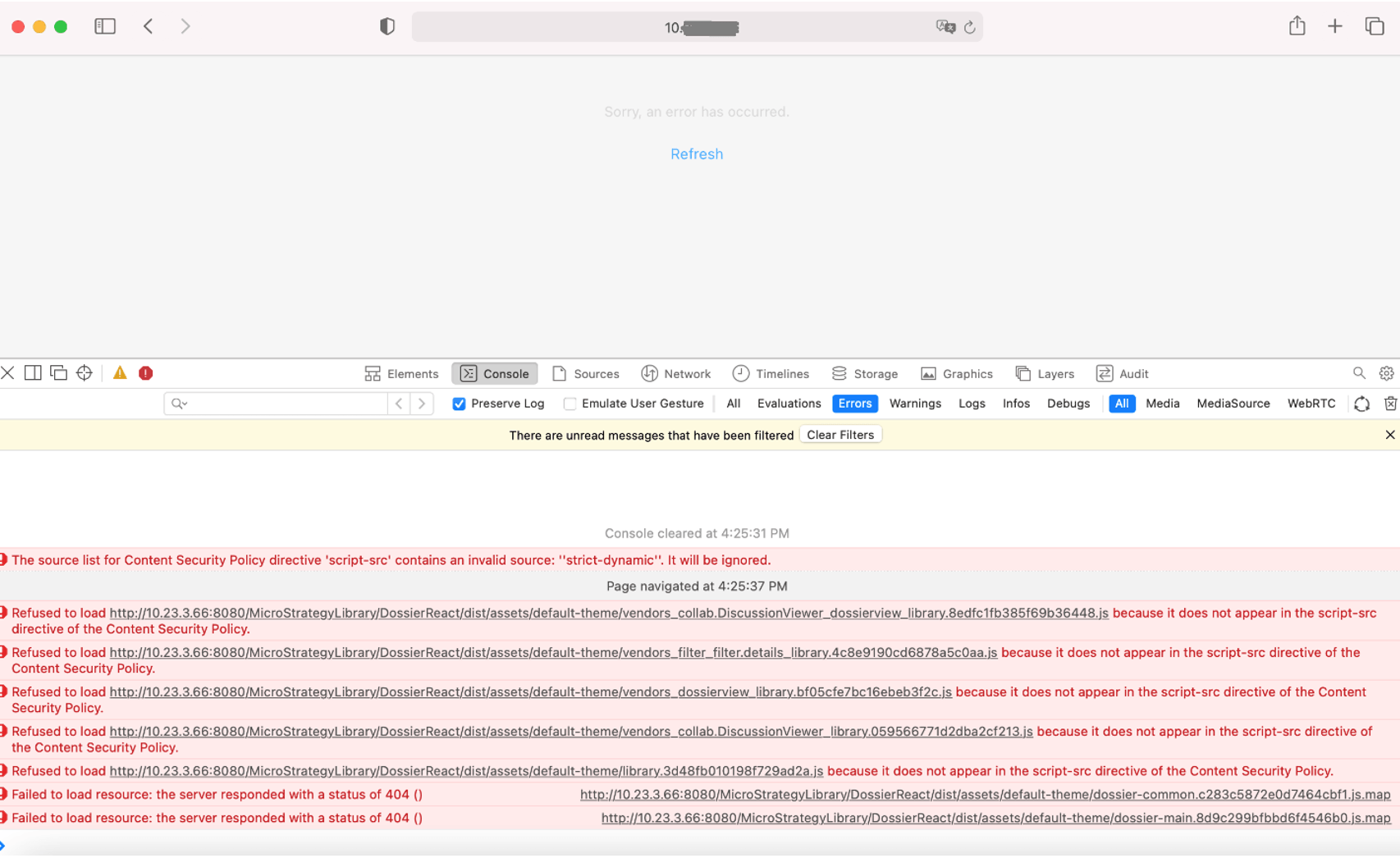
Sorry, an error has occurred.
Refresh
The following error can be observed in the browser’s Console tab:
The source list for Content Security Policy directive ‘script-src’ contains an invalid source: ‘strict-dynamic’. It will be ignored.
Refused to load … because it does not appear in the script-src directive of the Content Security Policy.
The issue only happens in Safari and the same works in the other web browsers such as Chrome.
The error in the console means ‘strict-dynamic’ is not supported by the web browser.
In Strategy Library 2021 Update 4, Content Security Policy is enabled and configured like this by default:
Content-Security-Policy: base-uri 'self'; object-src 'none'; script-src 'nonce-NONCE_TOKEN' 'unsafe-eval' 'strict-dynamic' https:;
Users can use one of the following solutions to fix the issue:
security.csp.policyDirectives=object-src 'none'; base-uri 'self'; script-src 'nonce-NONCE_TOKEN' 'unsafe-eval' 'strict-dynamic' https: http:;