Organizations gather a tremendous amount of data on systems access and authorization, but because this information is siloed by the application or system that generates it, it often goes unused. Usher Professional empowers organizations to analyze this data and turn it into actionable business and security insights.
Tap into identity intelligence:
The data generated from enterprise security tools, including identity, user behavior, and security information, is known collectively as identity intelligence. This data is extremely valuable but often underutilized because it is spread over multiple, disparate systems. Since Usher merges physical and logical access in a single solution, it eliminates this problem by providing one environment for all security and authentication data. Organizations can leverage this identity intelligence data to enhance their security posture, boost business performance, and eliminate unnecessary expenditures.
Analyze activity across the enterprise:
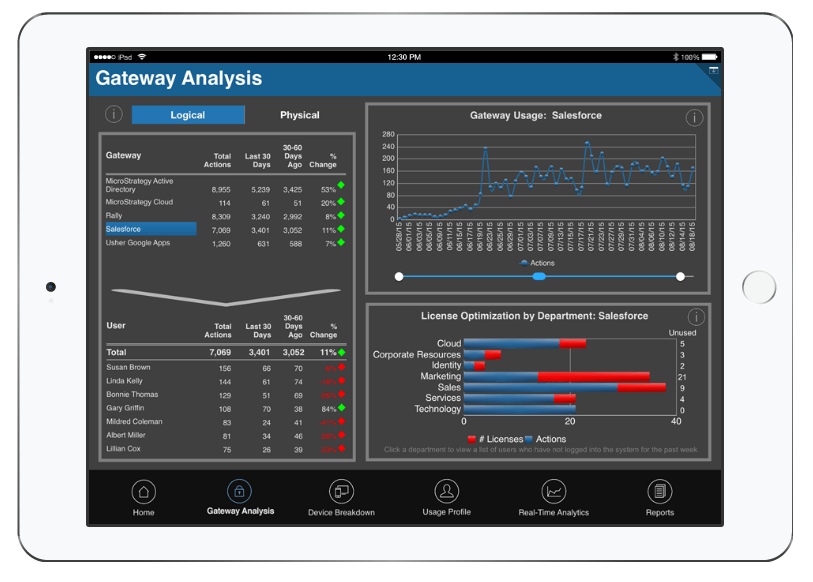
Want to see when and where employees are accessing resources? The Usher platform comes with powerful tools to analyze user activity data across the enterprise. With a large library of interactive graphs and visualizations, it’s easy to explore information, build dashboards, and create custom reports. Usher also takes care of all ETL processes, so access and authorization data generated on the back-end is automatically loaded into a data warehouse and leveraged by a pre-built data schema.
Usher Pro Discovery: