Introduction:
Lightweight Directory Access Protocol (LDAP) is a protocol designed for Directory Server access based on the X.500 OSI model. A Directory Server such as Microsoft Active Directory is the most commonly used method of storing user information across an organization or user base. Rather than creating users manually within Strategy, administrators may wish to be able to use their existing Directory Server to perform authentication and other access checks.
LDAP Integration for the Strategy Intelligence Server allows for the authentication of user credentials on the Directory Server, and the importing of user information into the Strategy Repository. The biggest advantage of this setup is that it alleviates the need for users to have a different username and password to access Strategy applications.
To setup LDAP Authentication for the Strategy Intelligence Server, users should follow the steps outlined in the following Strategy Knowledge Base technical note:
The LDAP authentication process as performed by the Strategy Intelligence Server is a three step flow:
A detailed explanation of the entire authentication process is available in the following Strategy Knowledge Base technical note:
Importing and linking Strategy Users and User groups:
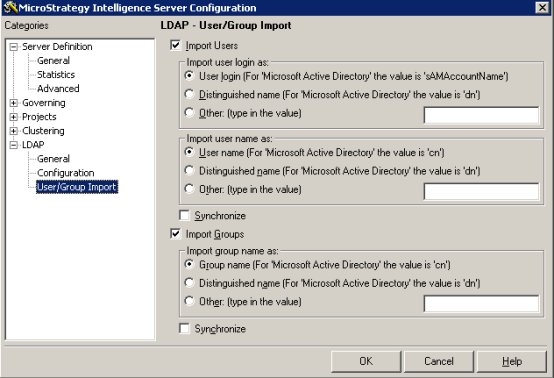
In the 'LDAP' -> 'User/Group Import' section of the Strategy Intelligence Server Configuration interface, administrators have the ability to specify the whether importing of users or groups must be performed for users logging into the Strategy Intelligence Server using 'LDAP authentication' as shown below:
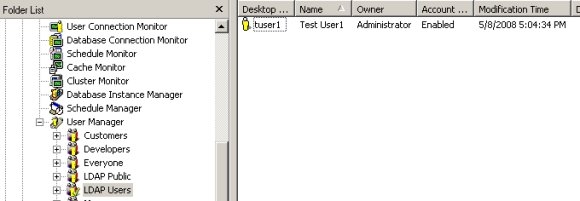
Besides the option to import users, it is also possible to link an existing Strategy user and/or group with a specific Directory Server user and/or group. The following explanations detail the behavior that may be observed for different combinations of the import settings:
LDAP Import Options:
LDAP Link Options:
The ability to import users and groups into the Strategy metadata from the Directory Server would be an efficient way to create or update a new Strategy user structure from an existing Directory Server. However, in the cases where there is an existing Strategy user structure and fewer users, a simpler strategy would be to link existing Strategy objects to their corresponding Directory Server objects.
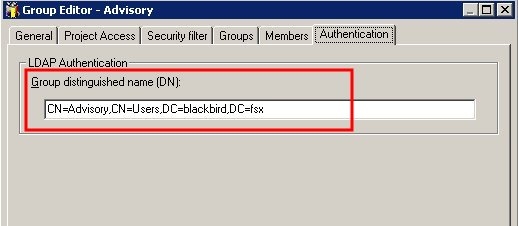
It is possible to link both Strategy Users and Groups from the User and Group Editors in Strategy Desktop. The link is the distinguished name (DN) for the Directory Server user or group to which the Strategy object will be linked.
Linking and Importing are not mutually exclusive. Linking a user does not affect the import options selected for LDAP integration, and a combined strategy of linking and importing may be used if appropriate. It is important to note that each Directory Server object can only be linked to one Strategy User or group. This means that if a Directory Server user has already been imported into Strategy, then another Strategy User or Group cannot be linked to that same user.
User/group synchronization:
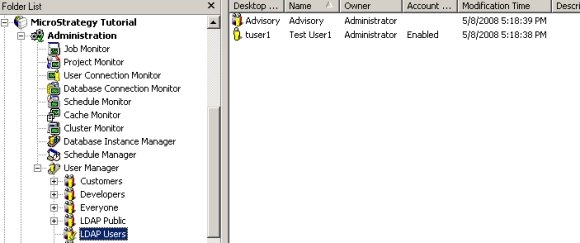
Whether users and groups are imported from or manually linked to LDAP entries, information in the Strategy metadata about these users and groups can optionally be updated at the time of login. The following user and group properties are subject to synchronization:
Synchronization checks the properties in the metadata against the corresponding attributes returned by the LDAP server. The LDAP attributes used are specified in the "User/Group Import" panel, under "Import user login as," "Import user name as," and "Import groups." These settings will be used even if user or group import is disabled; synchronization is an independent setting that may be used with or without import. If any properties in the metadata are different from what the LDAP server reports, the metadata properties will be changed to match.
When synchronization is enabled, the Strategy Intelligence Server can match users in the metadata to the LDAP credentials using the distinguished name OR the user login or full name. If, for instance, a user's distinguished name changes in the LDAP server, the user can still log into Strategy successfully as long as the login ID or full user name are the same. In this case, the LDAP's distinguished name saved in the Strategy user object will be updated.
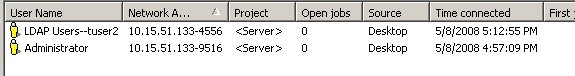
If synchronization is disabled, users and groups are identified in the Strategy metadata based on distinguished name only. Changes to the distinguished name in the LDAP server will cause users to be logged in as temporary users under LDAP Public privileges.
LDAP Public (Guest Connection):
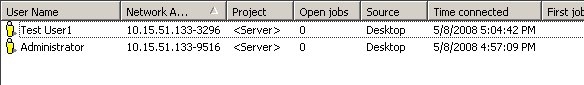
As a requirement for LDAP authentication through Strategy all users must have a valid login and password combination. If no password is specified by the user when attempting to login (or a blank password is used), regardless of the login information provided a guest user account session is opened on the Intelligence Server. The privileges granted to the guest session are inherited from the 'LDAP Public' group in the metadata.
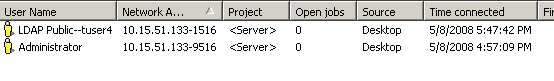
For Guest sessions, even if the Import User and Group settings are checked, no import action is performed by the Intelligence Server.