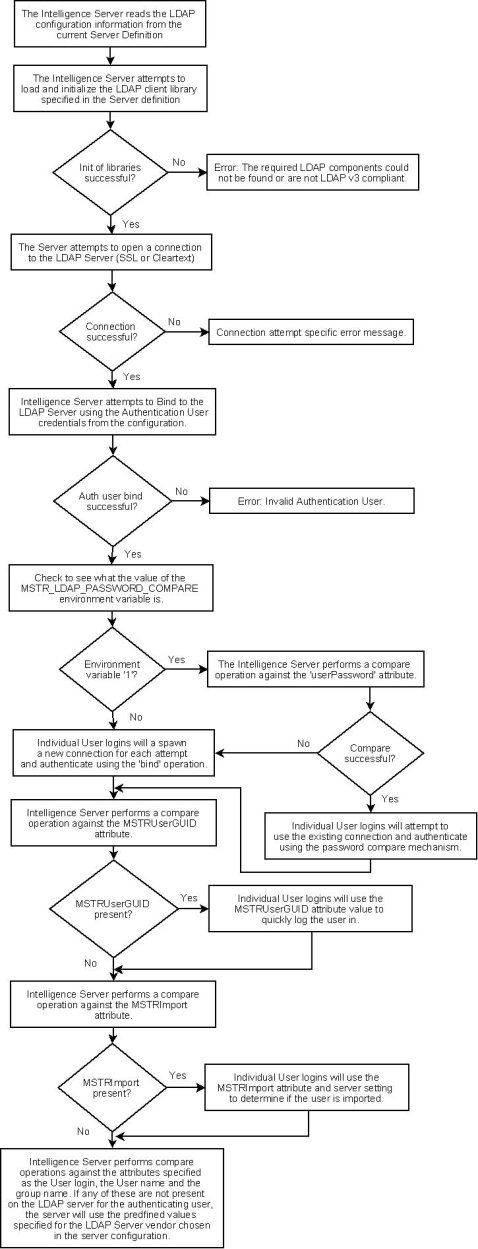
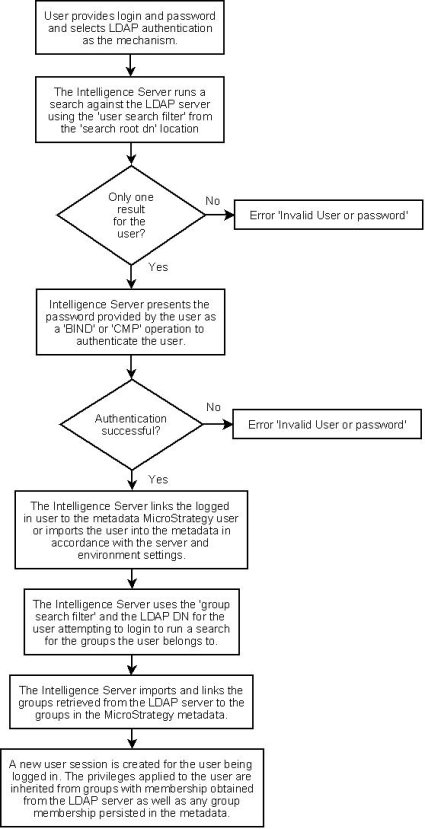
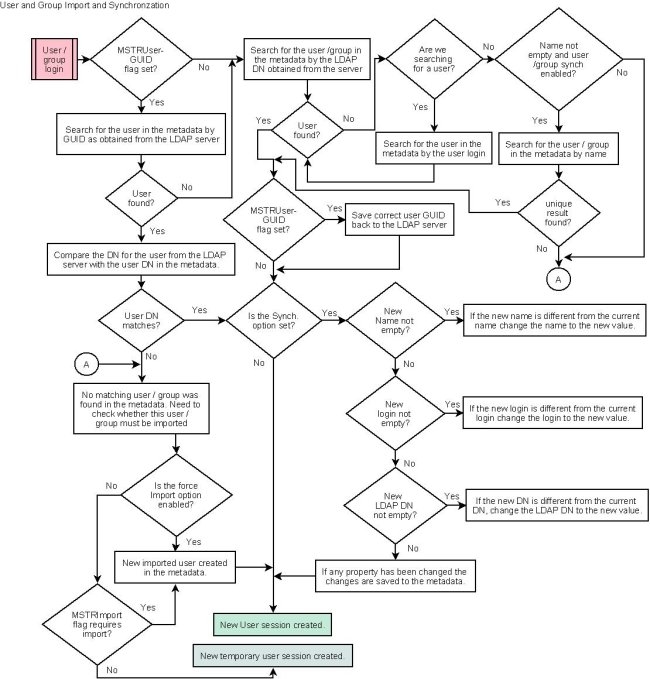
Users attempting to understand how the Strategy Intelligence Server integrates with the LDAP Server should refer to the following technical note for details:
This document attempts to provide a detailed look at the process flow involved in achieving this integration. This information may be used as a guide to understand and investigate issues that may arise when attempting to setup LDAP integration for the Intelligence Server. The typical issues that may be encountered related to LDAP integration with the Strategy Intelligence Server usually fall into the following two categories:
Strategy Intelligence Server LDAP integration FAQ
Q. Do LDAP users have their own Inbox and Personal folders?
A. If users are imported into the metadata, as Strategy users, they will have their own inbox and personal folders. If users are not imported, regardless of whether they are part of the LDAP Users or LDAP Public group, their inbox will only be persisted for the current session. Users that are not imported into the metadata will not have personal folders and will only be able to save to public folders if they have the correct privileges and permissions.
Q. What is the 'scope' value used for searching the LDAP Server?
A. The scope for all searches is for all nodes in the 'sub-tree'. The Strategy Intelligence Server 8.x does not support configuration of the scope parameter. Users may be able to limit search results using conditions in the search filter or by changing the 'search root' location.
Q. How can I assign security filters, security roles (privileges), or access control (permissions) to individual LDAP users?
A. Security roles and ACLs may be assigned to users after they have been imported into the Strategy metadata, this information is not assigned dynamically from information in the LDAP repository.
To allow users to dynamically inherit this information, administrators should assign these permissions at the group level in the Strategy metadata. User group membership information is dynamically determined each time an LDAP user logs into the system, regardless if they are imported.
For Security filters, the Strategy Intelligence Server 9.2.x and newer includes the ability to populate a 'System Prompt' object with the value of an LDAP attribute assigned to the user. This system prompt can then be used in a Strategy filter object, and used as a security filter as documented in the following Technical Note: KB35069 "How to link LDAP attributes to system prompt LDAP attributes in the Strategy Intelligence Server 9.2.x and newer releases"
Q. May two different users have different LDAP links, but the same user name?
A. No. The Strategy metadata may not contain two users with the same login name or user name. If an attempt is made to create a user with the same user login or user name the import will fail. Each user object in the Strategy metadata must have a unique User login or User Name.
Q. What happens if there are two users with similar descriptions in the LDAP directory?
A. If the DN (distinguished name) descriptor that specifies a particular user is not sufficient for the Strategy Intelligence Server to identify the user in the Directory Server, then the user will fail to log in. The administrator should enhance the 'user search filter' and 'Group search filter' in the LDAP configuration window to aid the identification of the user.
Q. What happens if I import a User Group along with all its members in the LDAP directory into a Strategy metadata and then assign a connection map to the imported group?
A. The connection map of the imported user group to which the user belongs will not readily apply to the user. The user needs to be persisted explicitly as a member of the group after she/he has been imported.