Users interested in setting up the Strategy Intelligence Server 9.4.x-10.x to authenticate users against a LDAP server should refer to the information provided in the following Strategy Knowledge Base articles:
These articles can help users to understand the various configuration options available for the Strategy Intelligence Server and the setup necessary for successful integration with a LDAP server.
Typically, LDAP integration issues within Strategy Intelligence Server usually fall into one of the following categories:
For troubleshooting LDAP setup and initial connectivity related issues, users should refer to the following Strategy Knowledge Base Technical Note for troubleshooting information:
KB18579: Steps to take to troubleshoot LDAP integration - connectivity and initial authentication from the MicroStrategy Intelligence Server 9.x-10.x
The article that follows below describes some typical error messages that may be seen when a user is attempting to login to the Intelligence Server using LDAP authentication.
The Incorrect login/password error:
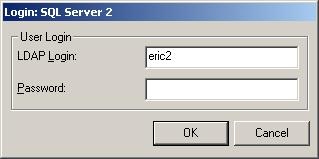
This error message is seen if the authentication user is able to successfully bind to the LDAP Server, but the user logging in cannot be found or authenticated on the LDAP Server side. The error messages found in the Authentication Server -> Trace log file can help diagnose the cause if the error. The following are the main reasons why this error message may be seen:
If syntactically incorrect search filter is passed to the LDAP server to perform the search, the Authentication Server -> Trace logs will display the following error:
2010-01-27 11:10:38.021-06:00 LDAP authentication trace: Failure in search LDAP user based on filter '(&(objectclass=person (sAMAccountName=hector1))' and search root 'dc=Strategy,dc=com''. (LDAP error 87: Filter Error)
2008-05-27 17:43:32.494-05:00 Login using LDAP with LDAP User='testuser1' 2008-05-27 17:43:32.525-05:00 LDAP authentication trace: no LDAP users are found to have the login with search filter '(&(objectclass=person) (uid=testuser1))' and search root 'DC=corp,DC=Strategy,DC=com'
2008-05-27 17:54:24.916-05:00 LDAP authentication trace: Failure in search LDAP user based on filter '(&(objectclass=person) (sAMAccountName=hector1))' and search root 'dc=Strategy,dc=com''. (LDAP error 1: Operations Error)
2008-05-30 13:44:09.224-05:00 Login using LDAP with LDAP User='hector1' 2008-05-30 13:44:09.334-05:00 LDAP authentication trace: user 'CN=hector1,OU=businessunit1,OU=test,DC=ads2003-labs,DC=Strategy,DC=com' failed in bind to LDAP server '10.16.17.58' on port '389'. (LDAP error 49: Invalid Credentials)
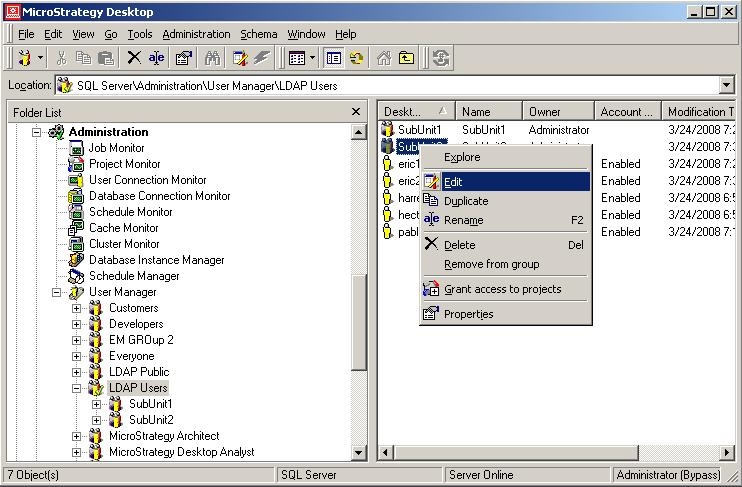
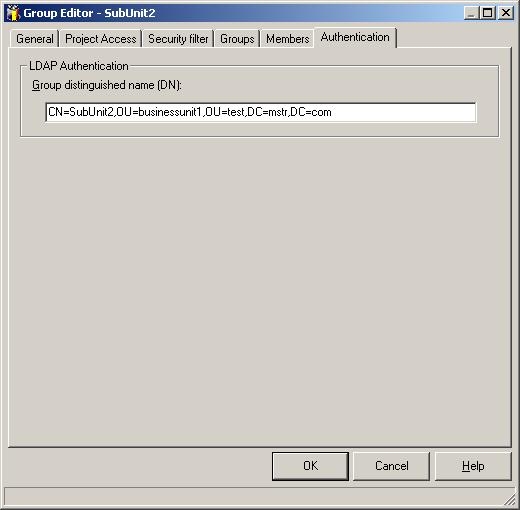
2008-05-27 17:50:29.572-05:00 Login using LDAP with LDAP User='hector1' 2008-05-27 17:50:30.728-05:00 LDAP authentication trace: this LDAP user belongs to the LDAP group, CN=SubUnit1,OU=businessunit1,OU=test,DC=ads2003-labs,DC=Strategy,DC=com
2008-05-27 17:50:30.853-05:00 LDAP authentication trace: this LDAP user belongs to the LDAP group, CN=SubUnit2,OU=businessunit1,OU=test,DC=ads2003-labs,DC=Strategy,DC=com
Anonymous Authentication:
If no password is specified when logging in to the Strategy Intelligence Server using LDAP authentication, the user is logged in as an Anonymous guest user. For more details see section 7 - Guest Connection in the Technical Note: