This article provides an overview of different technological challenges Strategy customers may face when migrating to BigQuery. For a PDF version of this article, please see the attached document. The list below contains the contents of this article:
Note: Starting in Strategy Update 10, Strategy supports temporary tables for Google BigQuery .
When migrating existing applications to BigQuery, certain Strategy capabilities are leveraged with tight integration of the databases. It is important to understand that certain capabilities powering the user workflows might not be supported in BigQuery.
Below are the common database workflows Strategy customers may encounter when working with BigQuery:
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
Below are unique BigQuery features that are not fully supported by Strategy:
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
samlAuthenticationRequestFactory samlAuthenticationRequestContextConverterSAML beans removed because samlAuthenticationRequestContextResolver is updated to use new class; please consider extending com.Strategy.auth.saml.authnrequest.SAMLAuthenticationAuthnRequestCustomizer to customize AuthnRequestrelyingPartyRegistrationResolvercom.Strategy.auth.saml.config.SAMLRelyingPartyRegistrationResolver no longer deduce registration ID from requests since it is done by callers; the exception is org.springframework.security.saml2.provider.service.web.Saml2AuthenticationTokenConverter, which we introduce a registration resolver wrapper com.Strategy.auth.saml.response.SAMLSSORelyingPartyRegistrationResolver which resolve registration ID from request for Saml2AuthenticationTokenConverter, then delegate the task to SAMLRelyingPartyRegistrationResolverBean nameChangesmstrSamlProcessingFilterSAML bean with base class replaced by Spring Security SAML provider builtin class: old: com.Strategy.auth.saml.response.SAMLProcessingFilter new: org.springframework.security.saml2.provider.service.web.authentication.Saml2WebSsoAuthenticationFilterforwardedHeaderFilter cookieProcessorFilter clientIDFilter redirectResponseFilterThese filters are defined in MainConfig.xml, some of which has the same name with filters defined in web.xml. They are renamed to avoid unexpected auto registration and duplicated filter names: forwardedHeaderFilter → mstrForwardedHeaderFilter cookieProcessorFilter → mstrCookieProcessorFilter clientIDFilter → mstrClientIDFilter redirectResponseFilter → mstrRedirectResponseFilter FeatureBigQueryStrategyAccess Control ListYesYesAutomatic TransactionsNoYesCustom Time ZonesNo*YesData PartitionsYes*YesMultiple Projects ConnectYesYes*Parameterized QueriesYesYesSurrogate KeysNoYesSQL Compiler OptimizationsNoYesUnlimited Updates per TableYes*YesUser Defined FunctionsYesYesFeatureBigQueryStrategyNested ColumnsYesNo*Geo ColumnsYesNo*Billing ProjectsYesYes |
*Limitations or workarounds are available in this article. Please see the following section for detailed description.
Access Control List specifies different levels of permissions that users and servers have to the database.
Impact: Security
Motivation: Role based access control in BigQuery is supported by Strategy Access Control Lists (ACL).
Details: BigQuery and Strategy both support ACLs. To learn more about ACLs in BigQuery, see the BigQuery ACLs documentation. To learn more about controlling user security in Strategy, see the Strategy documentation.
Atomic transaction is a concept where the DBMS supports begin and commit transaction updates. For example, for customers with a high volume of transactions, there needs to be a way to remove transactions from the datasets when the transaction has failed. Atomic transaction makes sure no dirty data is left in the system.
Impact: Transactions, Data Marts
Motivation: Atomic transaction is an integral part for some customer workflows.
Details: Strategy supports begin and commit transactions. BigQuery does not support atomic transactions at this time. To learn more about the limitations, see Atomic Transaction and KB483603.
Custom time zones help with managing time differences between different regions. For example, a worldwide organization can have custom time zones for different countries they operate in.
Impact: Internationalization
Motivation: Customers need to add logic to accommodate regional time differences.
Details: BigQuery only uses the UTC time zone, but other time zones can be achieved by using standard SQL timestamp functions. See Google’s documentation on using multiple time zones to achieve this functionality.
Data partitions works by dividing logical databases or tables into different unique parts to achieve the same result by solving smaller sub-problems. They can improve query performance and cost optimization.
Impact: Performance, Cost
Motivation: Queries run faster while only breaking the billing across the columns that are read.
Details: BigQuery is a columnar storage and only charges for the columns read when the query is running. BigQuery currently has a limit of 4,000 partitions for a partitioned table. See KB483965 for instructions on how to query table partitioned by ingestion time.
Multiple projects connect gives users access to more than one namespace (project) in BigQuery.
Impact: Operational
Motivation: BigQuery has different namespaces (projects) to accommodate different departments.
Details: Customer can specify additional project parameters in the BigQuery connection driver to work with multiple projects. Strategy does not support same name table names from multiple projects. You can work around the Strategy limitation by using views in BigQuery.
Parameterized queries process SQL instructions and user input while passing the data at run time. The SQL statement uses different key identifiers that are later supplied by DBMS. Parameterized queries protect the system against different attacks, i.e. SQL injection attacks.
Impact: Security, Performance
Motivation: To keep systems secure and easy to manage, it is a critical component for some customers.
Details: Parameterized queries are not enabled out-of-the-box in Strategy and BigQuery. However, you can still use them. See this docum
Surrogate keys are used in databases as a unique identifier for an entity or object in the database.
Impact: Operational
Motivation: Customer will have to add a logic if their application heavily uses surrogate keys.
Details: BigQuery only supports natural keys; using surrogate keys can be achieved by following Google’s documentation.
SQL compiler optimization helps generate faster SQL by join order optimization.
Impact: Performance
Motivation: SQL optimization is a generic feature widely implemented in DBMS solutions.
Details: Customers migrating from certain databases (i.e. Teradata), experience slow performance due to a lack of sophisticated join order optimization in BigQuery. Many database compilers optimize the query before running in case Strategy does not provide the most efficient query for that database. BigQuery does not have certain SQL compiler optimizations yet. See recommendations from Google on optimizing your query.
Limited updates per table puts a restriction on how many updates you can do in a table.
Impact: Transaction, Analytic SQL Passes
Motivation: Transactional reports are a key component for some customers.
Details: Even working around the atomic transactions limitation with BigQuery, there is still a hard limit of 1,000 updates per day for a table. Google allows you to bypass this limit on demand. See Google’s documentation to learn more about the limitation. See KB30257 to learn more about scenarios where you have to create a table and write back with inserts.
Impact: Customizations
Motivation: User Defined Functions (UDF) provides re-usability by defining the business logic once.
Details: See UDF documentation for BigQuery to learn more.
Nested Columns is the concept of having tables within a column. For example:
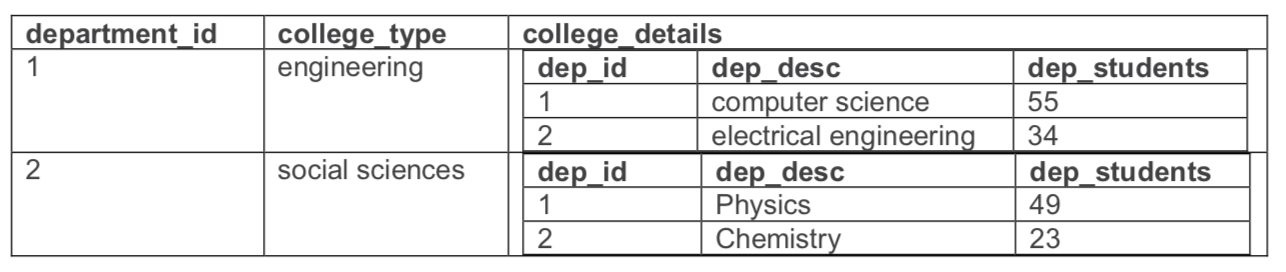
Impact: Performance
Motivation: BigQuery provides performance benefits with nested columns.
Details: The concept of nested columns is relatively new in the analyst community and it is sometimes difficult to run SQL queries against. Strategy does not support nested columns, but you can flatten the BigQuery nested column table as a view and then pass it to Strategy.
See Google's documentation on nested columns for more information. See KB483964 if you’re interested in how to workaround the nested columns limitation on Strategy.
Geo columns helps analyze geographical data in BigQuery. See BigQuery Geo Columns for more information.
Impact: Capability
Motivation: This is a unique feature in BigQuery to help customers with geospatial analytics.
Details: Geo Columns format is not supported with Strategy. However, Strategy has integration for longitude and latitude mapping for different mapping software, i.e. Mapbox and Esri maps. To learn more about how to use mapping software with Strategy please follow this Supporting map data and Geo Location .
Billing project helps with distributing the cost of the queries among certain departments.
Impact: Operational
Motivation: For operational convenience, customers like to leverage the billing project on BigQuery.
Details: Strategy does support billing project with BigQuery. As a workaround, the admin can change the DSN to a different project for billing purposes manually. To learn more about assigning Strategy users and groups to different billing projects, see KB484328. To learn more about the feature, see the BigQuery Cloud Billing documentation.
BigQuery’s pricing model is unique in terms of traditional DBMS solutions. Below are the three most common cost and performance related questions among Strategy customers.
For customers migrating from other DBMS solutions, Google recommends using the lift-and-shift approach to expedite data migration and then optimizing the tables if needed for better performance. If time and resources permit to redesign ETL, Strategy recommends redesigning the data model to take full advantage of BigQuery. See BigQuery for data warehouse practitioners for best practices for data warehousing.
Google recently improved their join performance, necessitating users normalize and denormalize data based on a case-by-case basis. See Google’s documentation on optimizing your table structure.
Google is constantly making changes to BigQuery, so keeping up to date with their release notes is critical.
The general recommendation Strategy has for cubes is to use them when data is going to be proactively aggregated and used constantly without frequent updates.
Strategy recommends a live connection for one-time use cases and small dataset requests that do not burden the system by importing a lot of data from BigQuery.
Below are some of the other benefits associated with each approach considering performance, security, and costs.
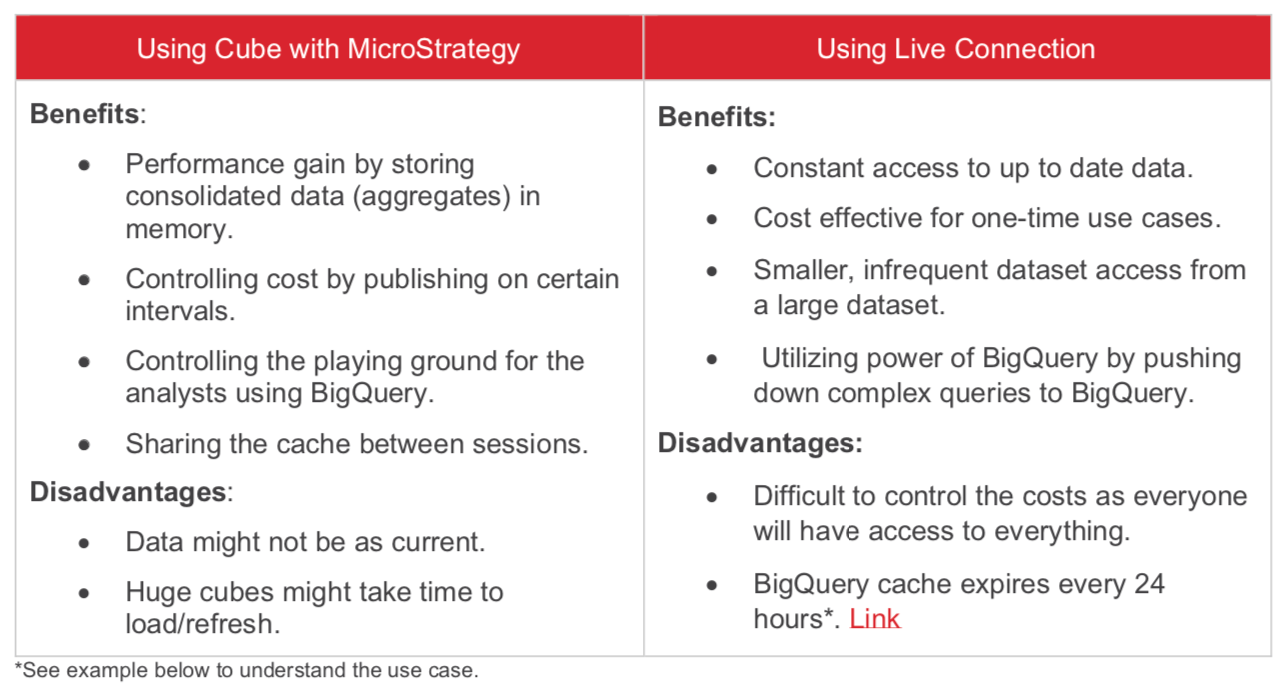
Example: Use live connect if you're trying to look at certain transaction details, such as transactions between 11:20AM UTC – 11:25AM UTC that originated from Virginia, and the product category Electronics.
Motivation: Direct and concise slice of data utilizing the power of BigQuery.
Example: Use a cube with Strategy if you're only concerned with last month’s aggregated data. The cube can answer most daily questions instead of going back to BigQuery.
Motivation: Updating cache once a month, using aggregated data, and saving on the cost by not querying data frequently in BigQuery.
Symptom: High Memory consumption or Out of Memory error.
While fetching string data from BigQuery to Strategy, the driver imports the maximum size (~16KB) of BigQuery rows into the in-memory cache if no string limit is defined. Strategy recommends reducing the string length size to the minimum of the maximum length of the database column’s size. This reduces the amount of data imported in Strategy's in-memory cache. This is important because, by default, the BigQuery driver imports the maximum size for rows if no limit is defined.
Tuning can be achieved by changing the driver settings for both ODBC and JDBC. See KB483973 to achieve this optimization.
Connectivity is typically the biggest concern among customers. To better assist Strategy customers, Strategy has created documentation with the latest information.
How to connect to Google BigQuery with MicroStrategy
Strategy recommends using the ODBC and JDBC driver shipped out-of-the-box with the installer. These drivers, developed by Simba, work by passing the query to BigQuery and returning the result to Strategy, leveraging the query interface for BigQuery. Both drivers are shipped with 2019 Update 3 or later and leverage the BigQuery High Throughput API (large scale ingestion mechanisms), which gives performance improvements of at least 10x compared to earlier versions. For steps, see the documentation on enabling the drivers.
Starting in Strategy 2020 Update 2, both the JDBC and ODBC drivers support User Account Authentication through OAuth 2.0 mechanism.
Please refer to the table below to see the different features among the drivers:
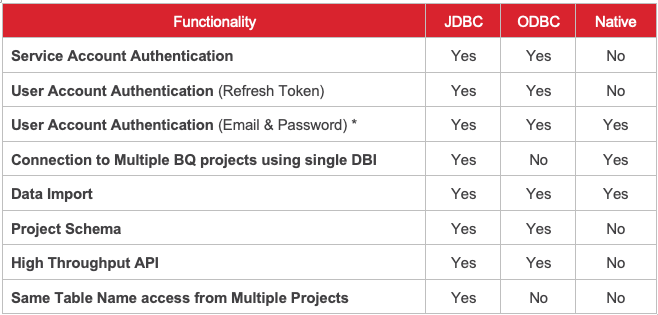
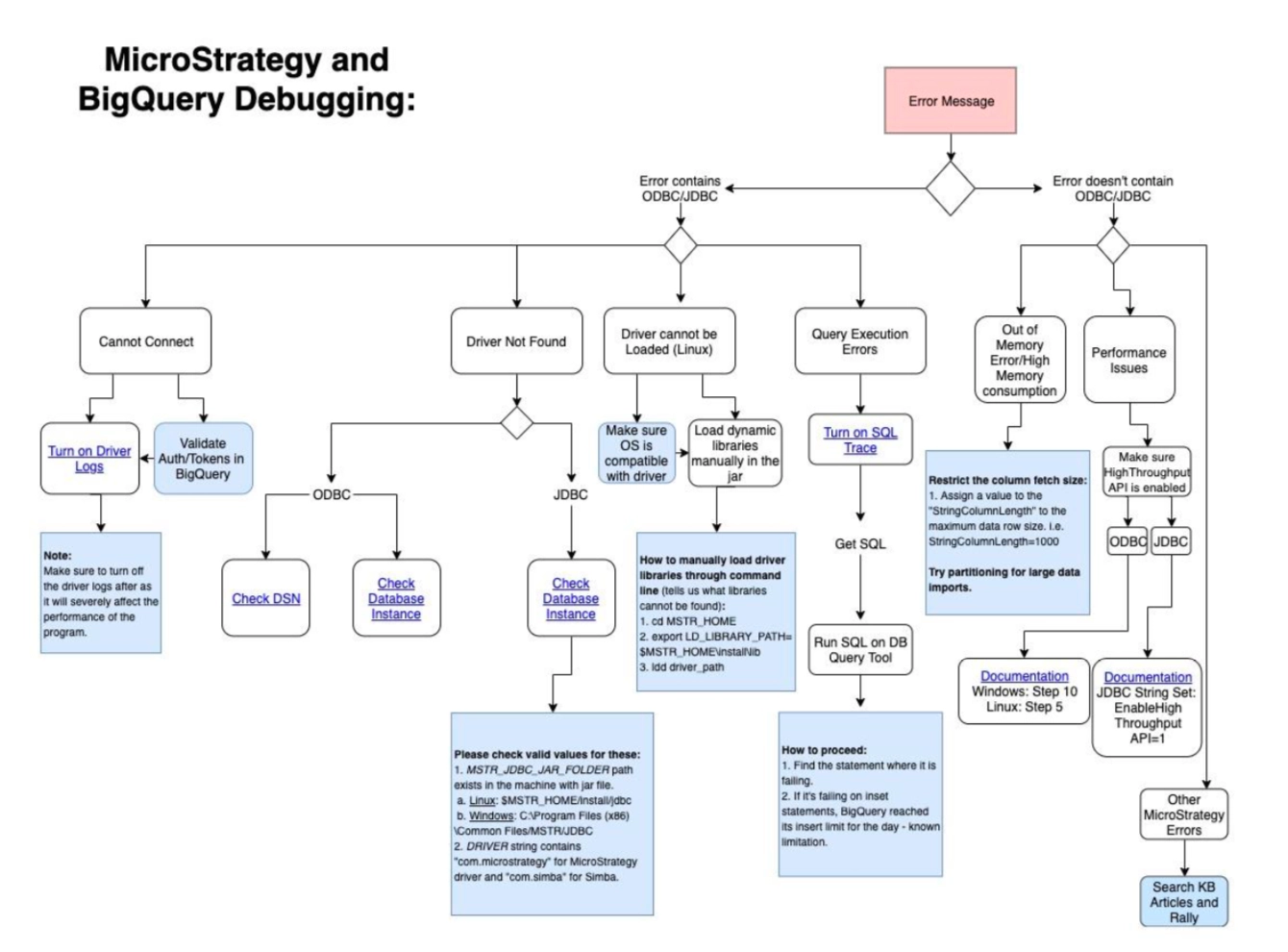
This workflow diagram can be found in KB483877.
Please reach out through the Community Site.
Please log a case for Strategy.