In March 2020, Microsoft Active Directory in an upcoming Windows security spdate will introduce more security for LDAP channels. Windows Active Directory integration with Strategy will require you to have SSL enabled.
For more details on the upcoming Windows security update, refer to KB484049: Impact of Microsoft Active Directory Changes on MicroStrategy Installations.
For instructions on how to implement LDAP over SSL (LDAPS), refer to the following KB articles:
For Red Hat Linux, the library file is
libldap.so.For example, the specific library name and version for a Red Hat 5.3 will look like:
/usr/lib64/libldap-2.3.so.0.
/usr/lib64/libldap-2.4.so.2.
MSTR_LDAP_LIBRARY_PATHvariable in the
LDAP.shfile located in the
$MSTR_HOME_PATH/env directory.
# locate --basename 'LDAP'
$ ping linuxldapserver.domain.com
cacert.pem'. Ideally this should be an absolute path so there is no confusion about where the server is looking. For example,
/var/opt/MicroStrategy/ldap/cacert.pem.
cacert.pem)has to be placed within the working directory of the Intelligence Server:
<MSTR_HOME_PATH>
Intelligence Server.For example,
/var/opt/MicroStrategy/IntelligenceServer.
As highlighted in the following screenshot:
cacert.pem.
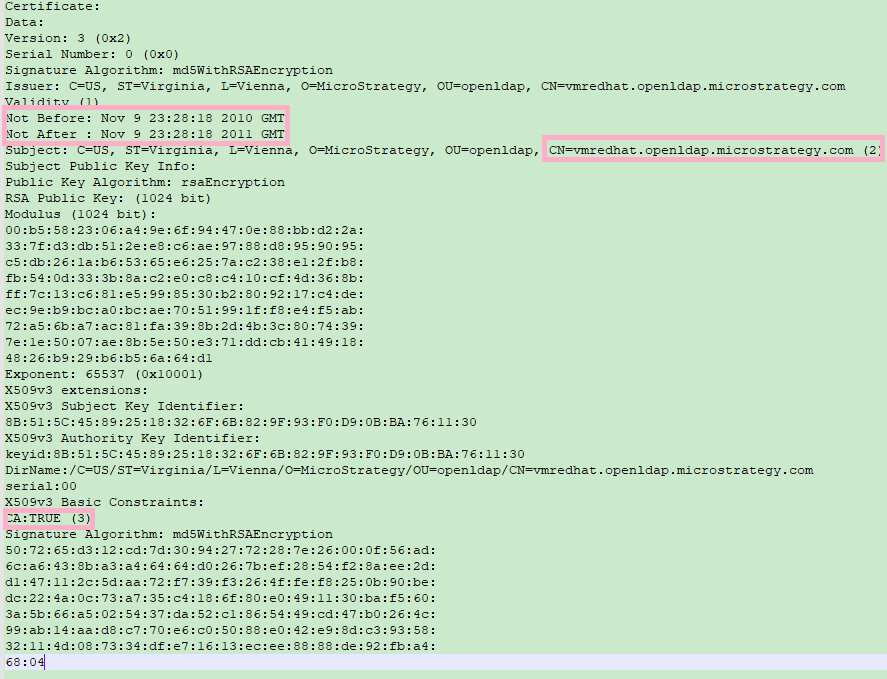
$ openssl x509 -in
-noout -text
$ openssl x509 -in /var/opt/MicroStrategy/ldap/cacert.pem -noout -text -inform PEM
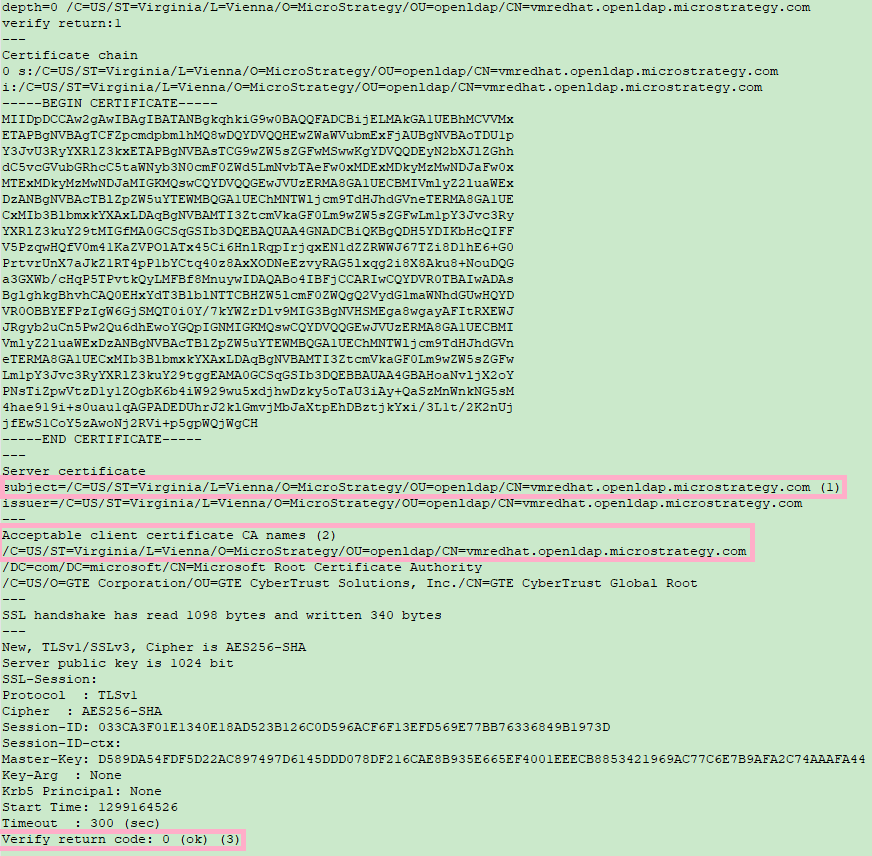
$ openssl s_client -connect
$ openssl s_client -connect
:
-showcerts -CAfile